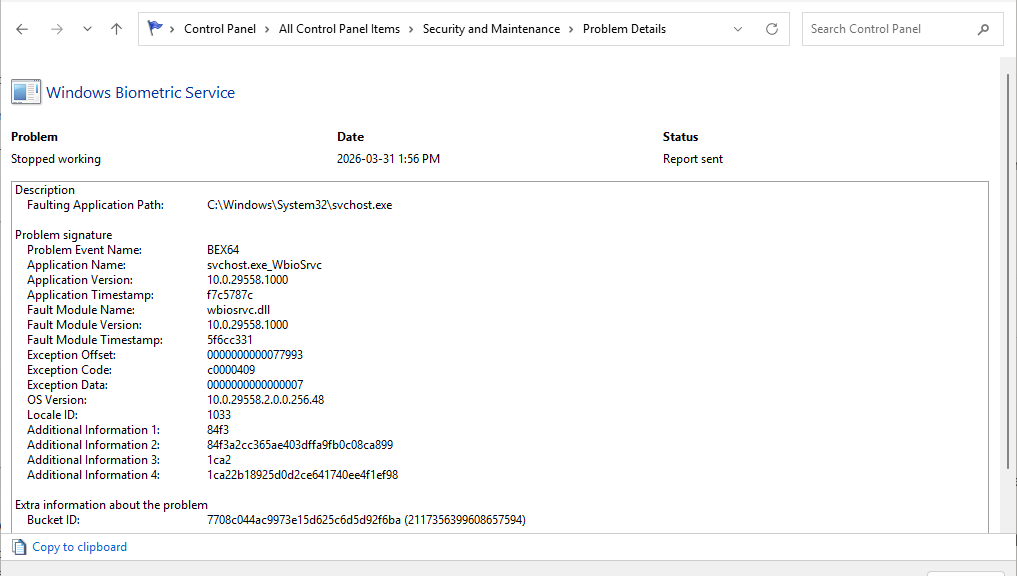
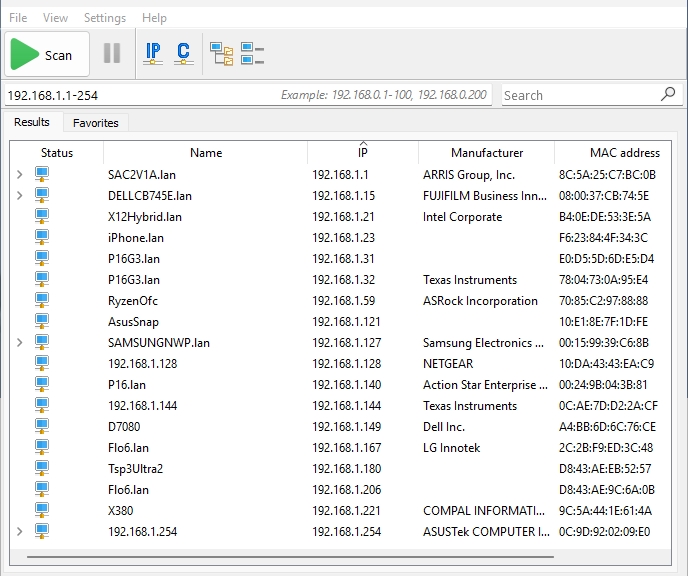
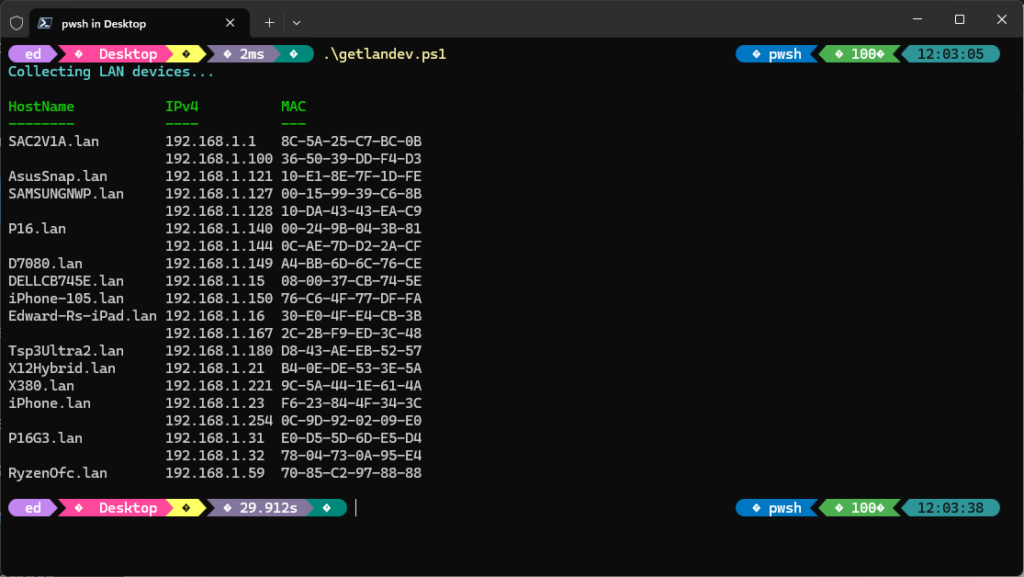
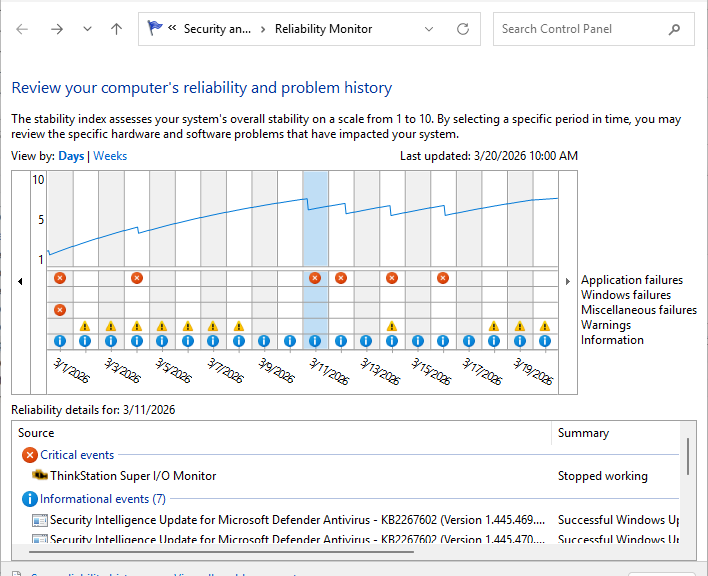
I have to laugh at myself a little ruefully. In checking over my Canary test platform just now — the snazzy little ThinkPad X12 Detachable Gen 1 hybrid tablet — I found the too-familiar BEX64 error in the mix. To those not already aware, this flags an out-of-bounds memory access, often from a driver or an associated dll. In this case it was the notoriously picky Synaptics Fingerprint reader. After looking over driver dates and versions, I realized my driver was newer than the official Lenovo offering. Thus, rolling back fingerprint reader driver was exactly the right thing to do. But there was a problem, also of my own making…
The Problem with Rolling Back Fingerprint Reader Driver
I’m relentless about using Driver Store Explorer (RAPR.exe) to clean up old drivers. Needless to say, that means the Rollback driver button in the fingerprint reader’s properties sheet was greyed out. Of course, that’s because the older driver had been removed from the Store. So I had to visit Lenovo support and grab the driver from there. Easily done, armed with the unit’s Serial Number thanks to Lenovo Vantage.
Another complication then presented. Because I was replacing a newer driver with an older one, I had to uninstall the new before attempting to install the old. Why? Because Device Manager doesn’t allow older drivers to over-write newer ones as a matter of policy. That is, Windows enforces this to prevent accidental regressions or security downgrades, so it refuses to overwrite a newer driver with an older one unless the newer one is removed first. An uninstall gets the previous driver out of the way, so the new install can proceed successfully.
All’s Well That Ends Well
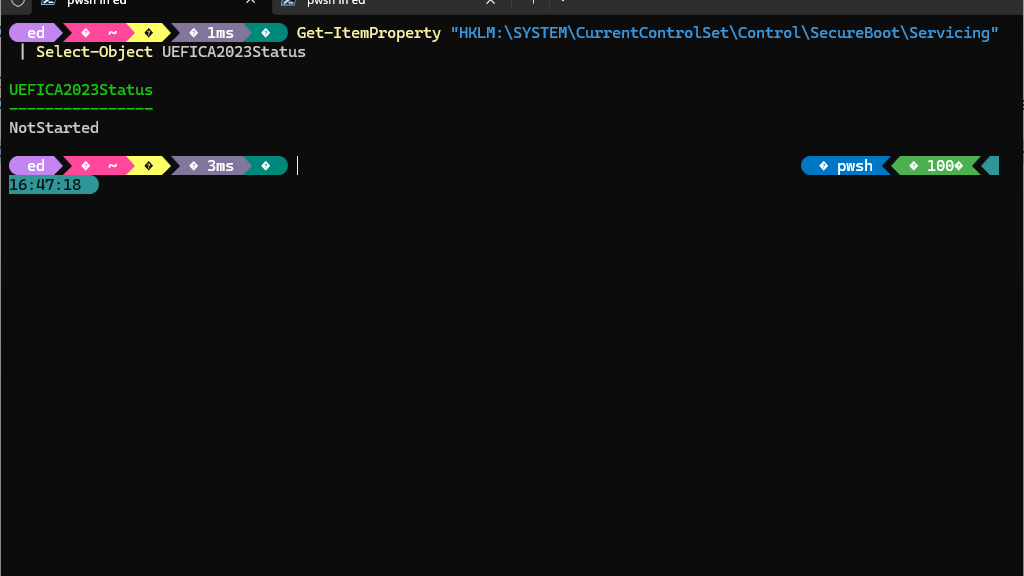
I’m 100% confident that the driver swap worked. I’m expecting the fingerprint reader to behave well going forward. What makes me so confident? After installing the driver, I logged out and then used the selfsame fingerprint reader to log back in. It worked, and read my right index fingerprint from the already-defined biometric data at its disposal.
If there had been any issues with compatibility or workability, Windows Hello would have forced me to start afresh. That would mean proving my identity with a PIN, password, or other acceptable data. Then, I’d have had to re-scan my fingerprints to give the reader something to work with to establish my identity.
None of this happened. The fingerprint reader worked on the first try. I’m hopeful this will do away with the error documented in this post’s lead-in graphic. But as with so many other things in Windows-World, we’ll just have to wait and see what happens. Stay tuned!