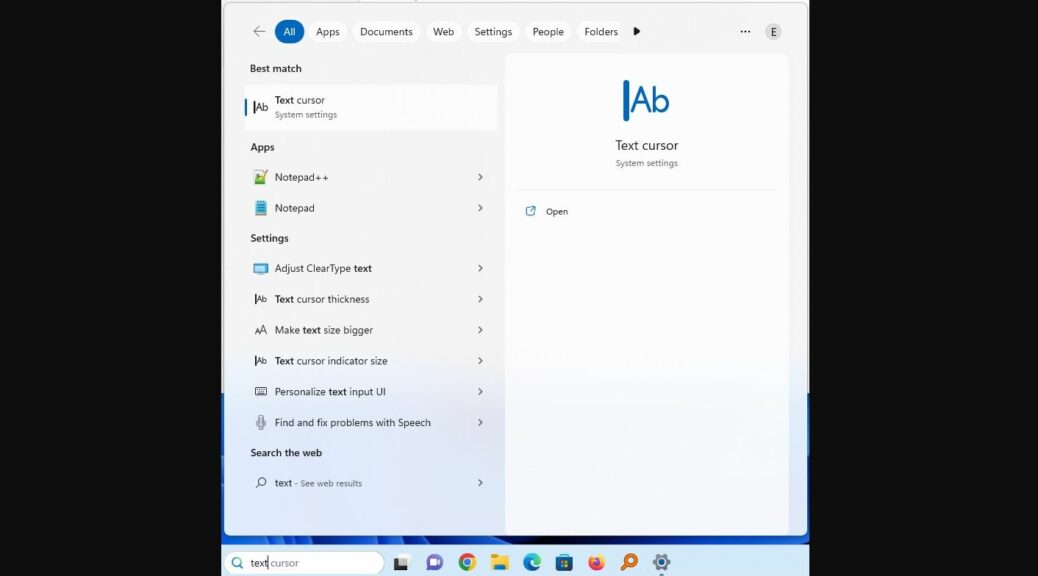
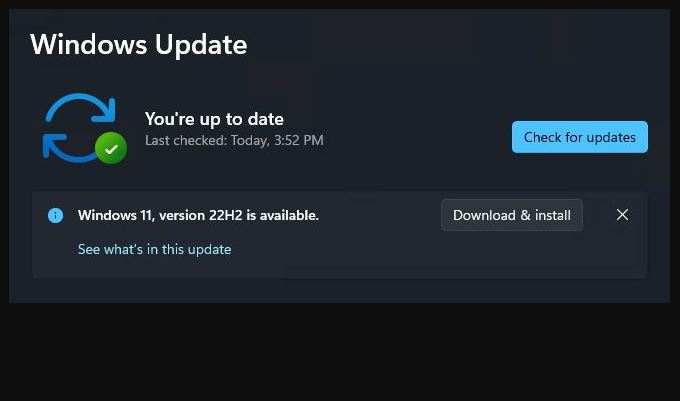
For some time now, my spouse Dina has resisted upgrading to Windows 11. Her 11th gen Dell 7080 Micro meets all of the hardware requirements. But she’s not ready to take the plunge. Thus, when somehow, someway Windows Update started the Windows 11 upgrade process on her PC, I got a little worried. I shouldn’t have bothered — part-way into the install process, the installer halted the upgrade. Why? Because of a compatibility hold, Start10 blocks 11 upgrade on that PC.
Easy Fix for Start10 Blocks 11 Upgrade, But…
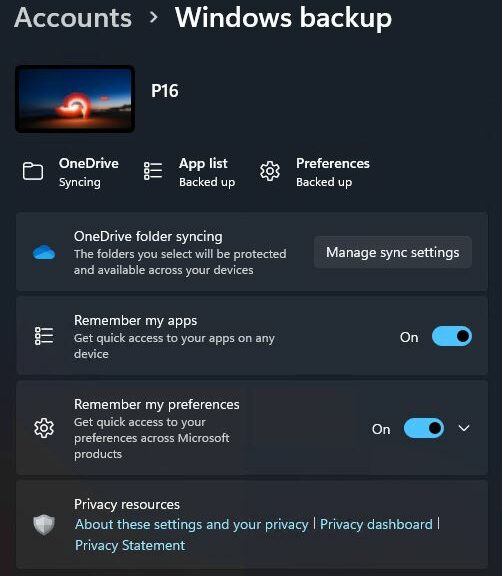
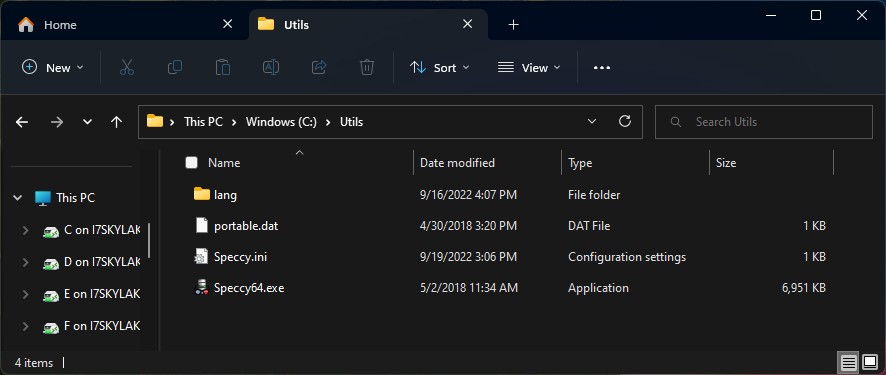
Yes, I know: if I were simply to uninstall Start10, the upgrade would proceed without further demur. Ironically, it serves as a form of insurance in this case. When Dina’s ready to upgrade, I’ll upgrade her (and install Start11 on the resulting build to minimize the impact of that change). That’s when I’ll take Start10 off the board, then…
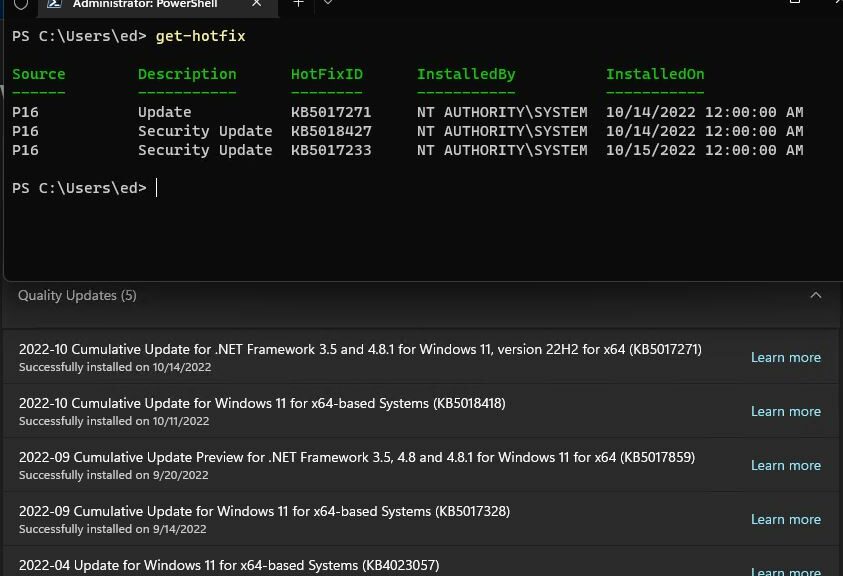
The frequently-offered upgrade got started somehow in the last week. Somebody must’ve clicked the “go-ahead” button without really understanding what was going on. If it happens again, I now know that the upgrade process will quit before it gets to the post-GUI install phase.
Shoot! It might even be the case that now the compatibility hold is known to the Windows Installer, it won’t even try again. I certainly hope so. But sometimes, here in Windows-World what looks like a curse is actually a blessing. Of course, that vice is often versa, so it doesn’t always (or only seldom) works in one’s favor.
Thus, I’ll revel in this surprisingly friendly turn of events. It will certainly help to preserve domestic tranquility here at Chez Tittel. It should also suspend the too-typical “What did you do to my PC?” that “The Boss” has been known to emit after Windows Update does its periodic thing on her machine.
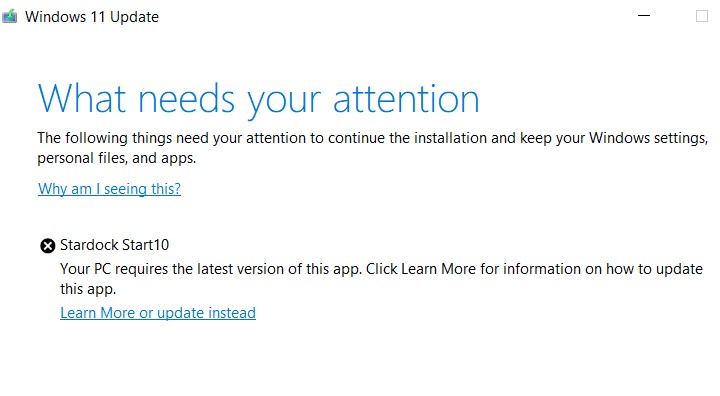 When this error shows up in WU, I can bail on the upgrade. Funny that it doesn’t screen in advance, but after downloading and during the GUI install phase (about 35% of the way in, if what the UI says is true). Go figure!
When this error shows up in WU, I can bail on the upgrade. Funny that it doesn’t screen in advance, but after downloading and during the GUI install phase (about 35% of the way in, if what the UI says is true). Go figure!