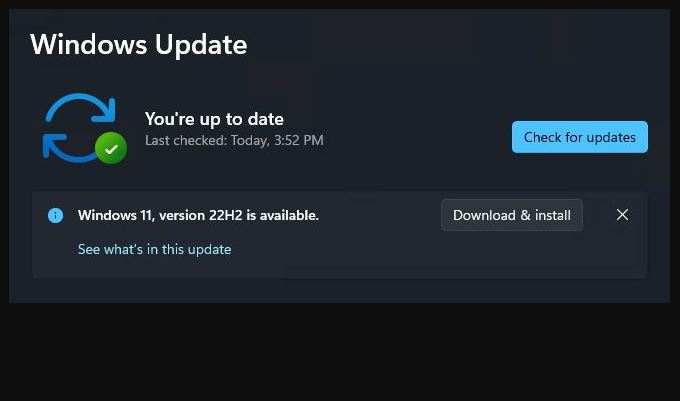
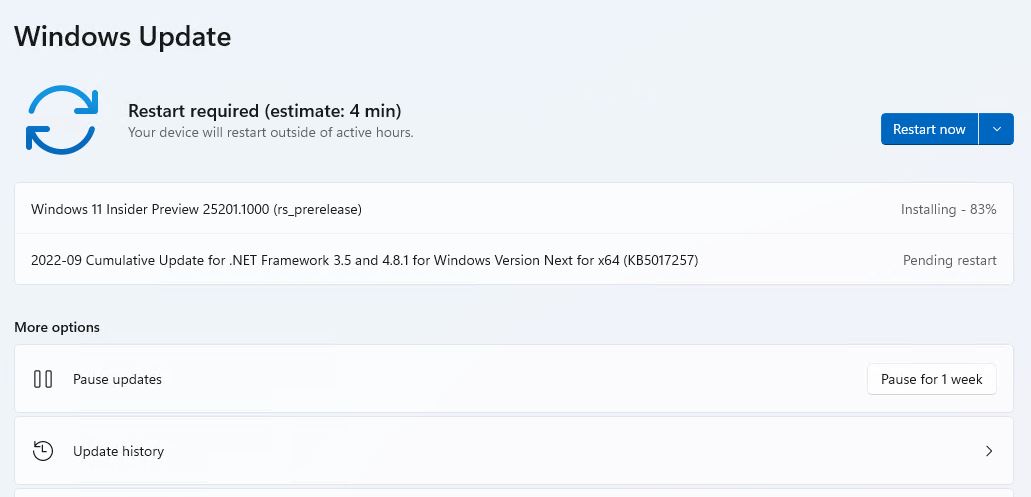
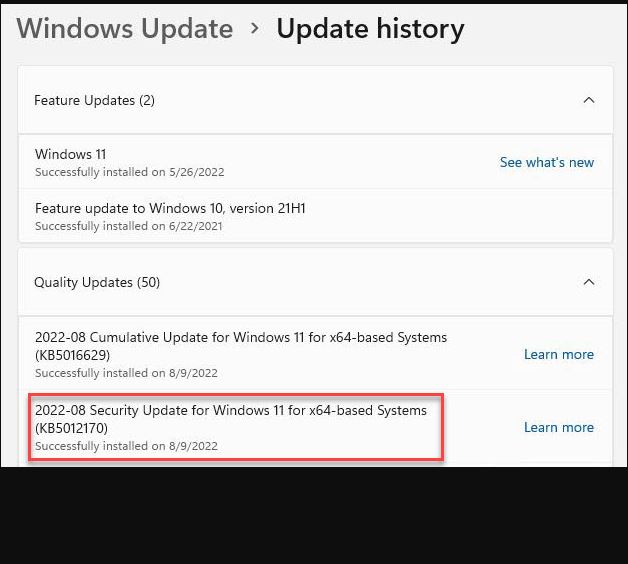
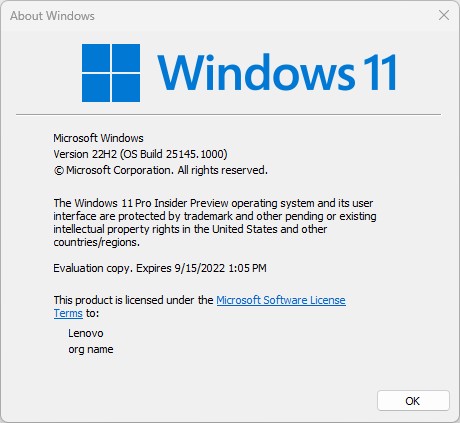
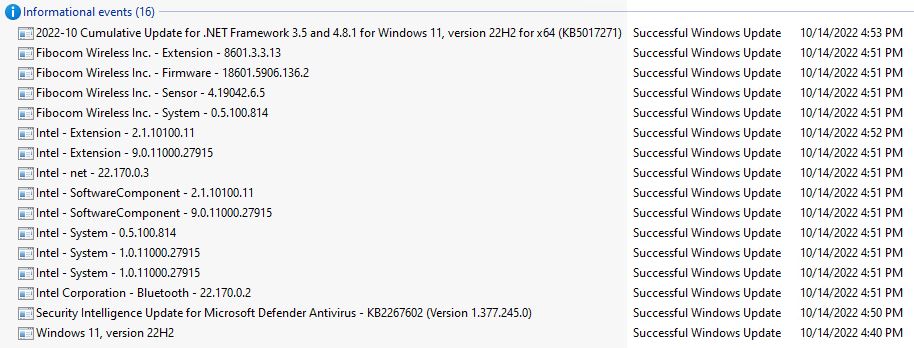
OK, then. I performed my daily ritual WU check on the P16 Mobile Workstation on Friday (Oct 14) . This time, the P16 safeguard hold lifted, and I was able to update to Windows 11 22H2. As you can see in the lead-in screencap, the 22H2 download was available during capture. Neat-o!
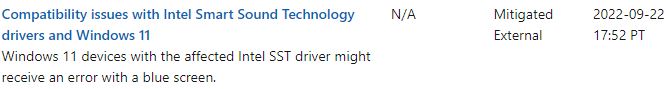
And indeed a quick visit to the 22H2 Known Issues page shows that my hold-up — the Intel SST drivers — appears as “mitigated.” Here’s what that looks like:
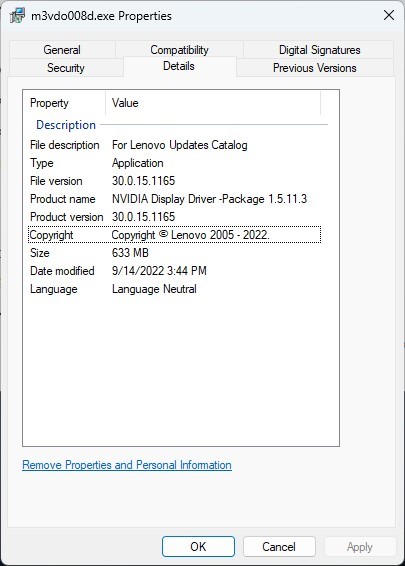
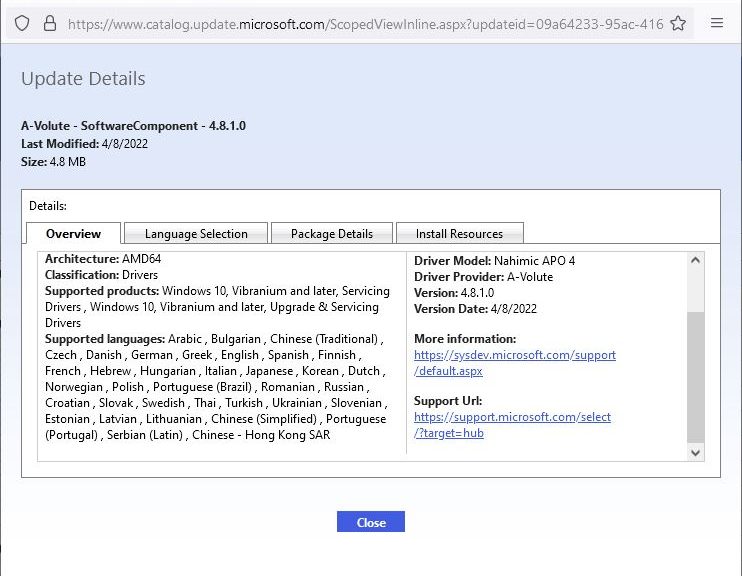
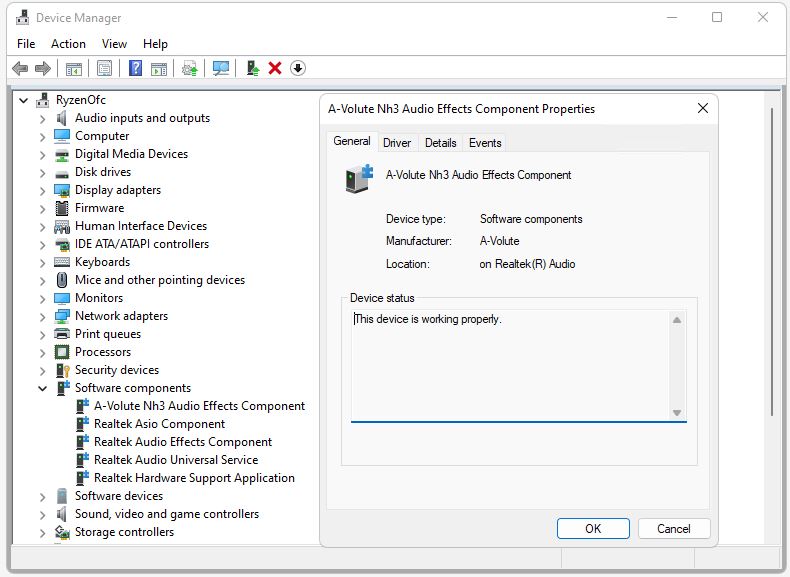
The P16 blocking issue is now resolved, thanks to Intel driver updates. These appear in DevMgr under the “Software Components” heading.
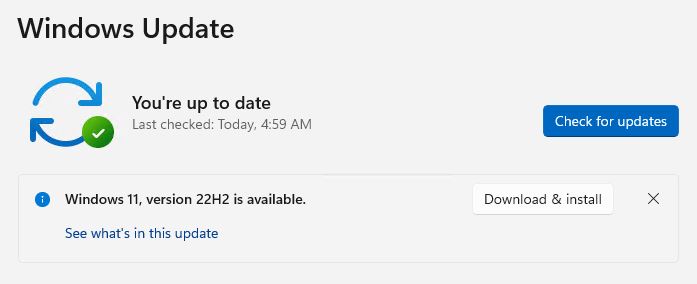
With P16 Safeguard Hold Lifted, Upgrade Proceeds
I got a little concerned right after the first reboot (from the GUI-based portion of the install, into the post-GUI phase). The P16 sat at 0% complete on processing updates for what seemed like an eternity (about 4 minutes). But then, it started to chunk through the process and finished in about 20 minutes during that install phase.
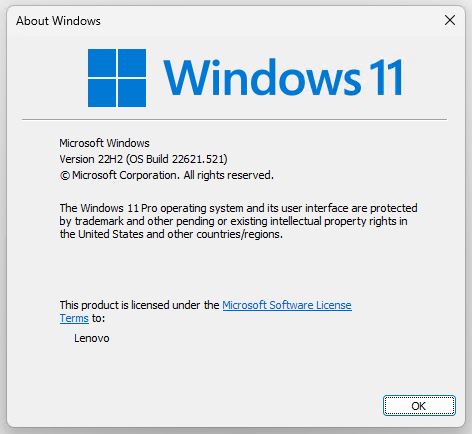
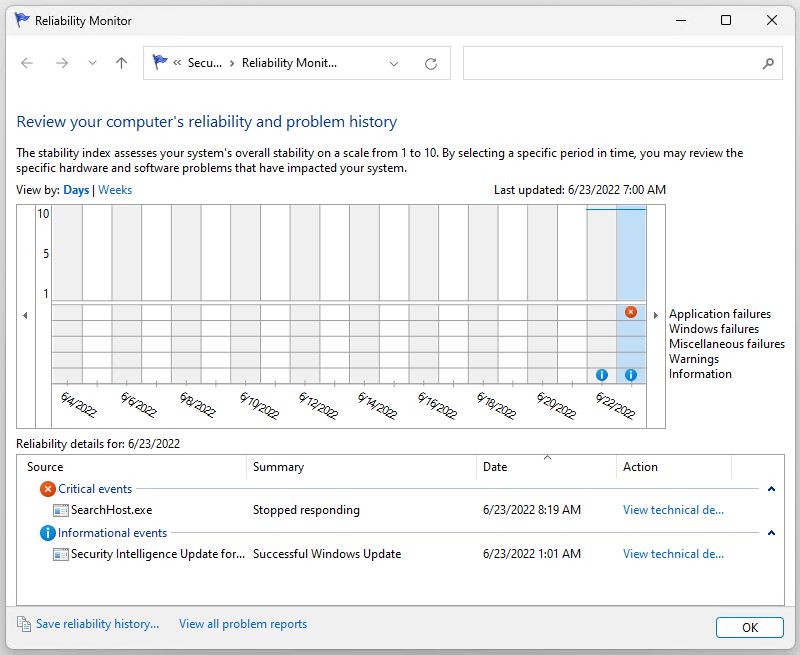
I noticed that the update included a raft of driver updates –14 in all — by checking Reliability Monitor later on. The two items of greatest import show up in the software components category where various sound -related items reside.
 Whatever the issue might have been, I’m glad to see it resolved. And so far, the P16 is running without apparent issues. I’m connected to it remotely via RDP right now, so that recent bugaboo is not present here, either. Good-oh!
Whatever the issue might have been, I’m glad to see it resolved. And so far, the P16 is running without apparent issues. I’m connected to it remotely via RDP right now, so that recent bugaboo is not present here, either. Good-oh!