It’s not like I’m unfamiliar with this sensation. No, not at all, based on oodles of history with phased feature roll-outs for Insider Previews on Windows 10 and 11. But Friday, I got bit for the first time on a Norton 360 upgrade. That translates into what I call a phased updates Norton 360 strike. Let me explain…
What Phased Updates Norton 360 Strike Means…
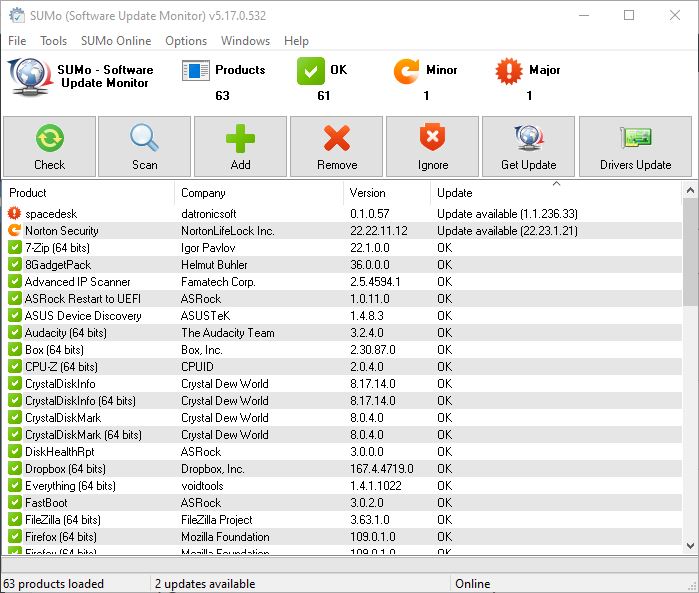
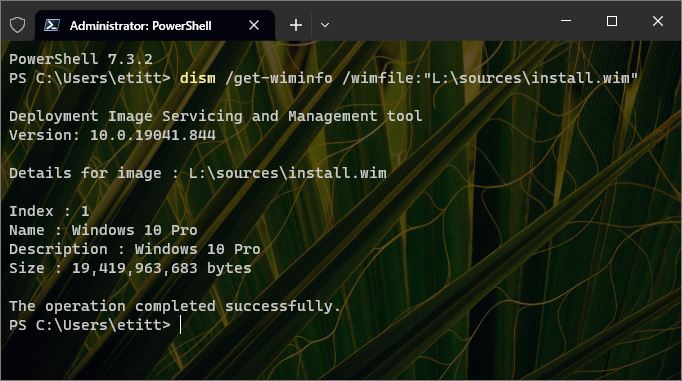
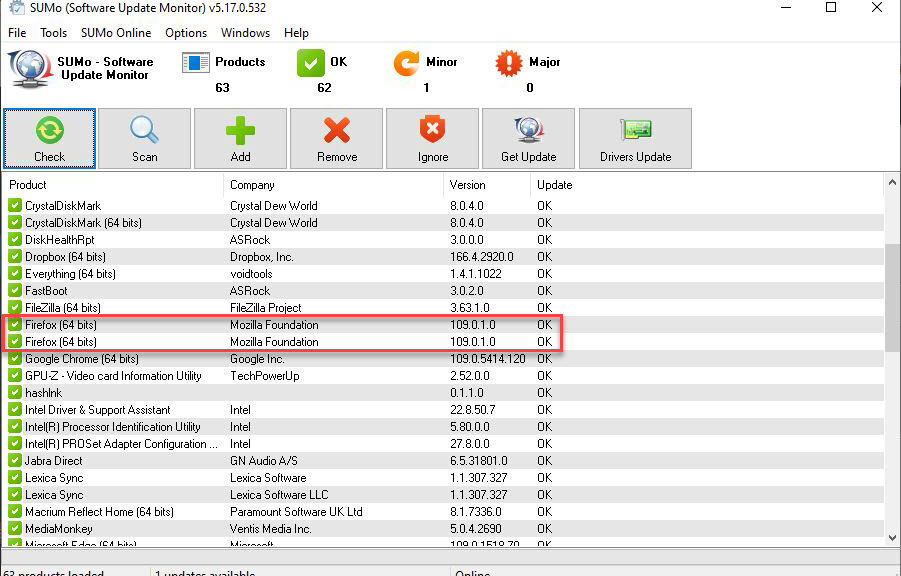
I found a Norton update notification dated February 4, 2023 online. It includes a telling sentence that reads in part as “…this version is being released in a phased manner.” Alas, SUMo doesn’t care: it thinks the release is generally available. So here’s what it tells me about my production PC:
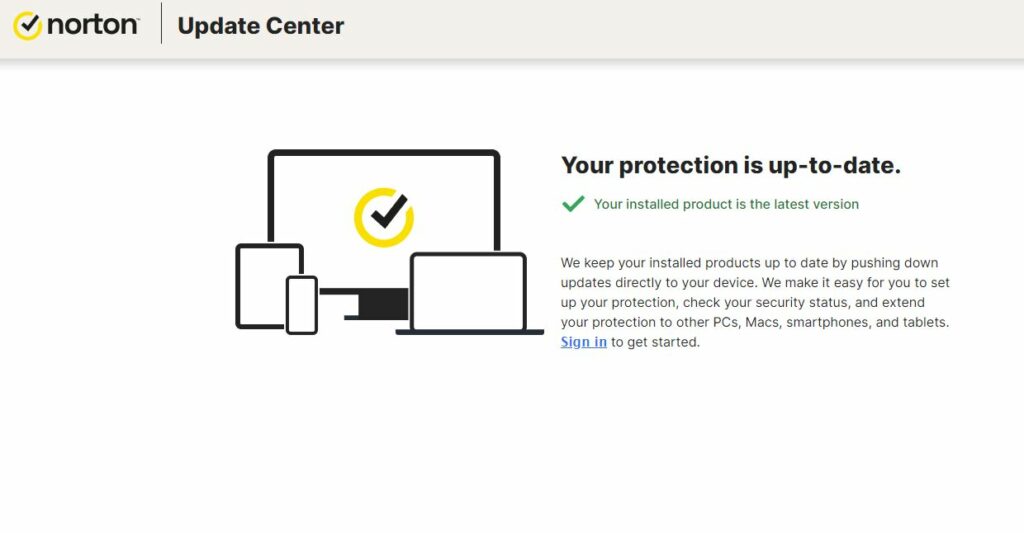
Notice the second (orange) item indicates that 22.23.1.21 is available. True enough in some general sense, but not true for my PC. Here’s what Norton tells me when I attempt to update it through the Norton Update Center:
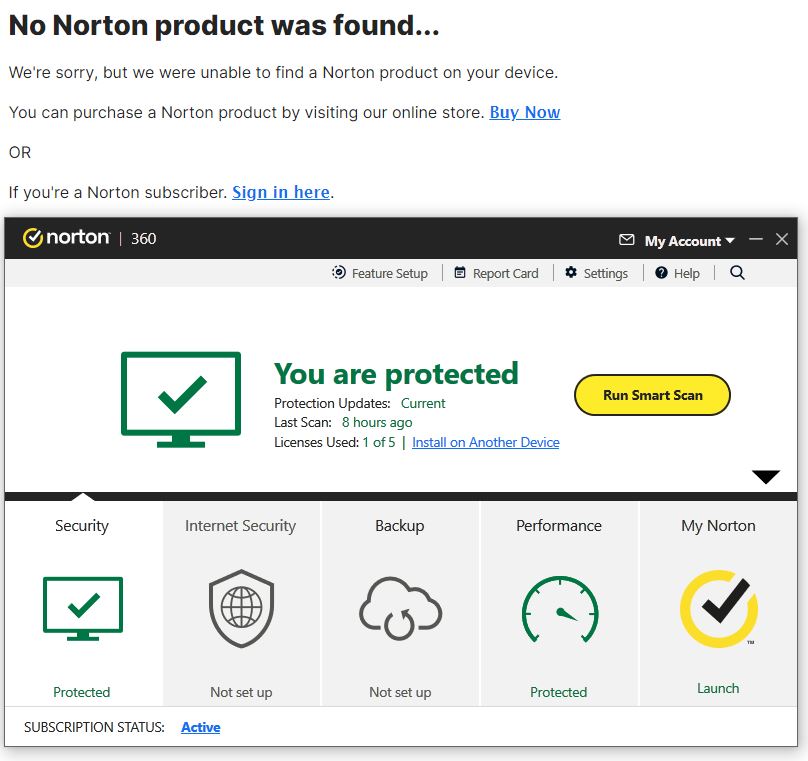 Just for grins, I positioned the open Norton 360 home window underneath the results of the Webscan that says “no product found.”
Just for grins, I positioned the open Norton 360 home window underneath the results of the Webscan that says “no product found.”
Trip a Little Reboot, and…
Of course, one can’t have the 360 window open without running said software. So I knew something was flaky about the Norton AutoDetectPkg.exe that I’d just downloaded. A quick reboot later, and the following message appears instead (and confirms my preceding hypothesis):
Am I Frustrated, or What?
Yes, indeed I am. But because I have long, sad and weary experience behind the curve on phased releases I know this means my turn has not yet come for release 22.23.1.21. I’ll wait as patiently as I can for same, since Norton won’t make it available any other way. Otherwise, I’d just force install it, and make the SUMo warning go way.
And boy howdy, is that ever the way things go sometimes, here in Windows-World … with a bullet, this time!
Note added February 22
In the past little while (it’s been 9 days since I wrote this post), Norton has quietly updated itself to the new release. Here’s what the about information says now (notice the version number: indeed, it is now at 22.23.1.21).
My phase has come in the form of a recent and silent upgrade to 22.23.1.21.
‘Nuff said!