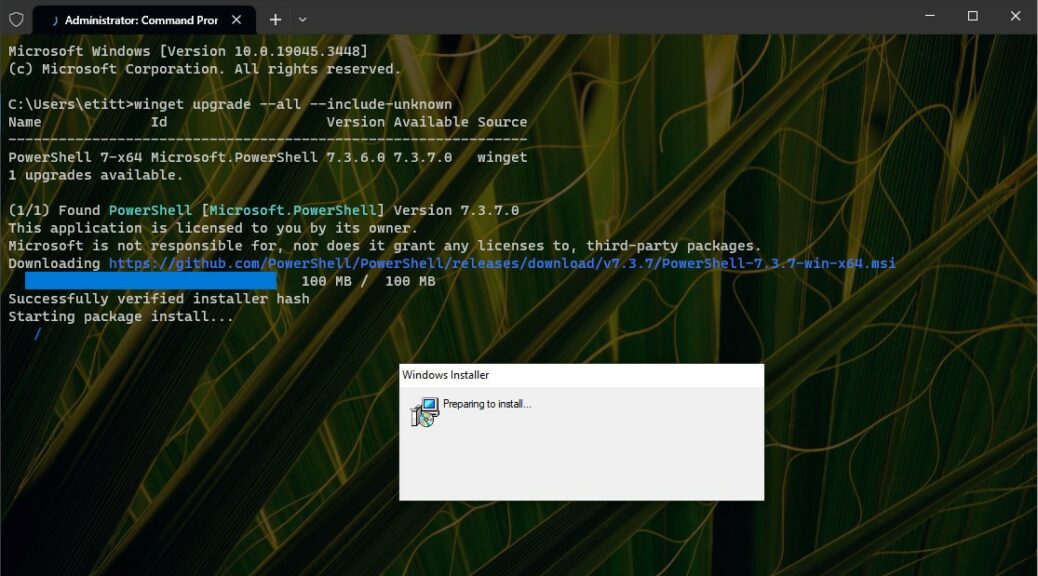
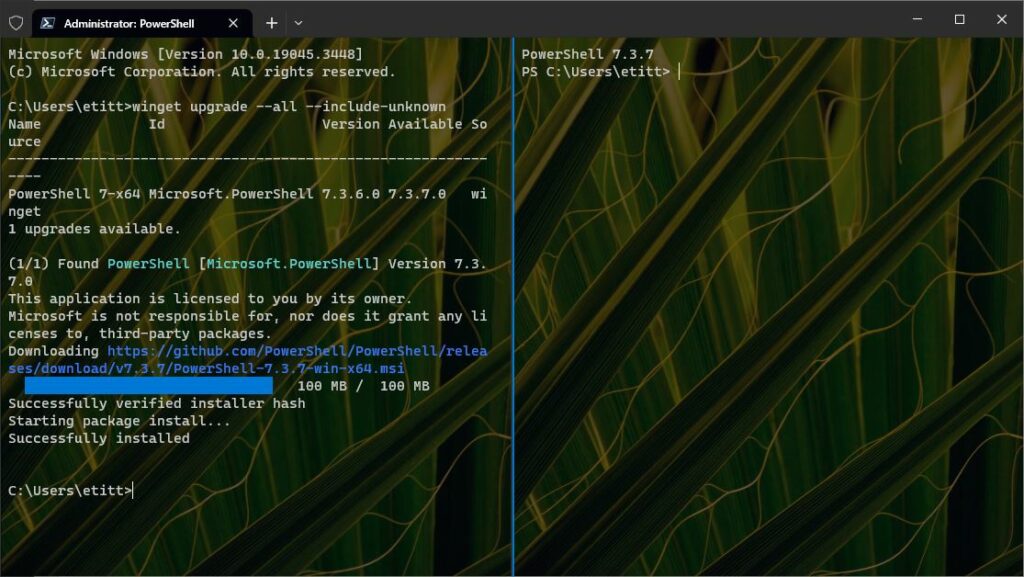
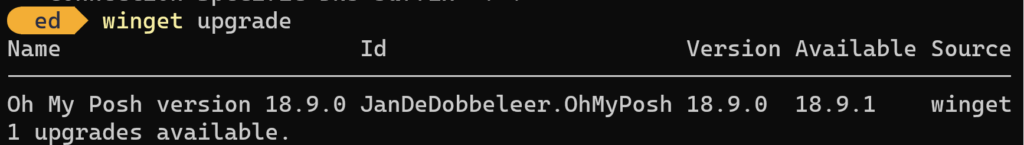
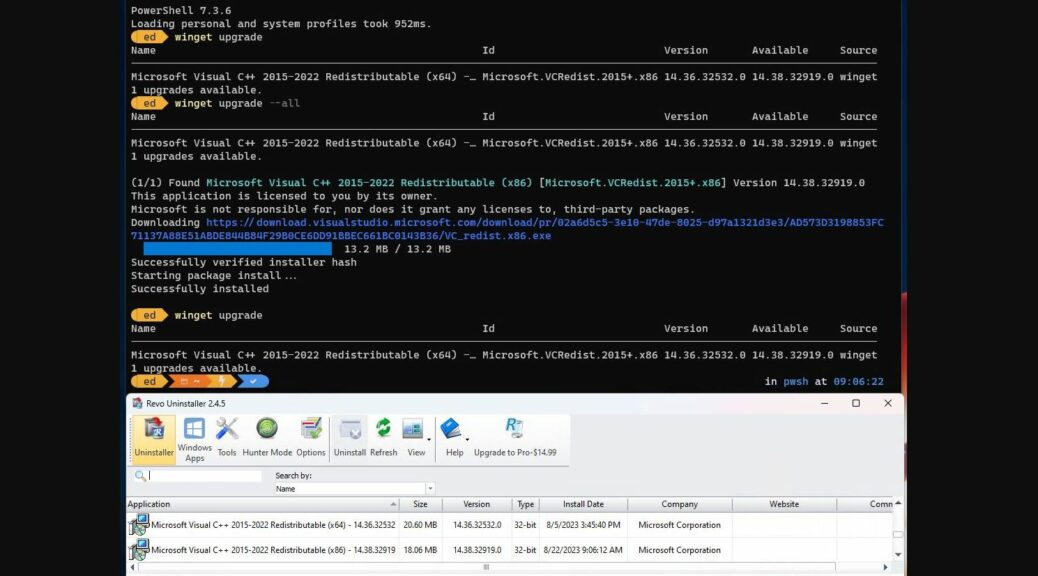
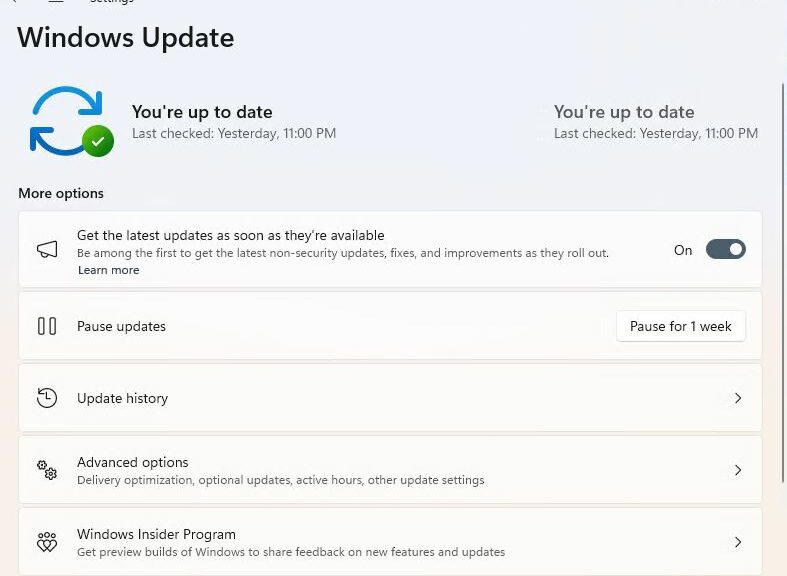
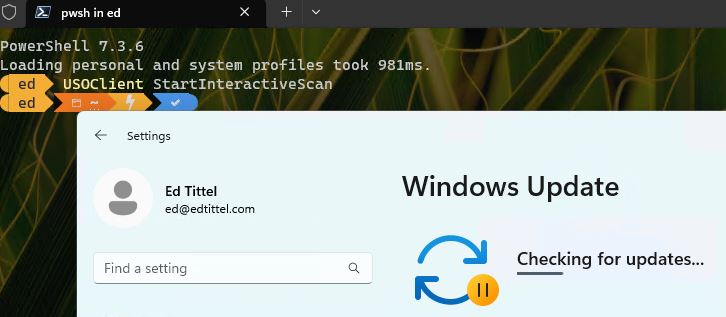
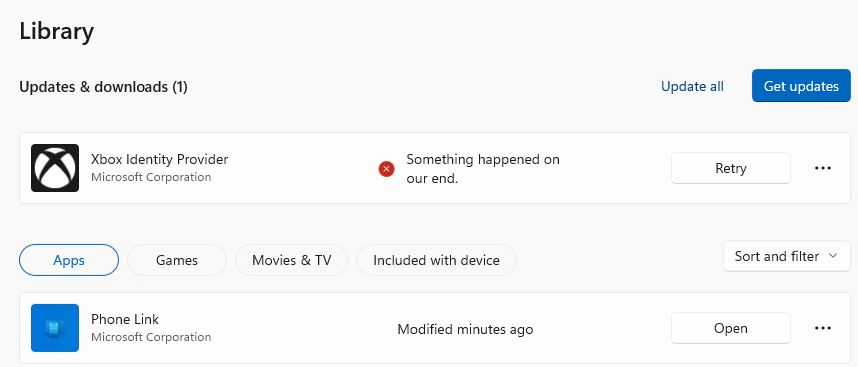
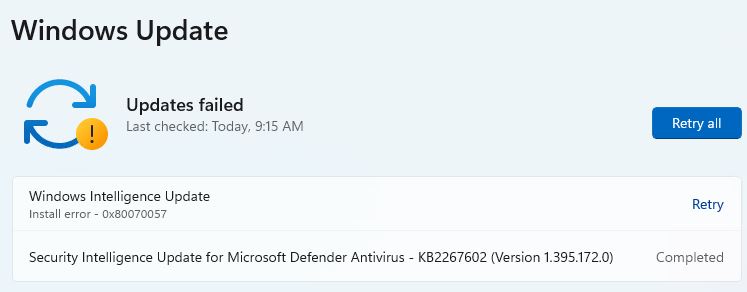
As part of my daily Windows routine, I run the winget package manager to keep most of my applications up-to-date. Occasionally, I’ll also check in on the MS Store to see what it’s been finding and updating on its own. As the spirit moves me, I sometimes click the “Get updates” button to spur its actions along. I find myself appreciating Microsoft’s update ecosystem more and more (yes, even WU) as I work with it constantly. Let me explain…
Why I’m Appreciating Microsoft’s Update Ecosystem
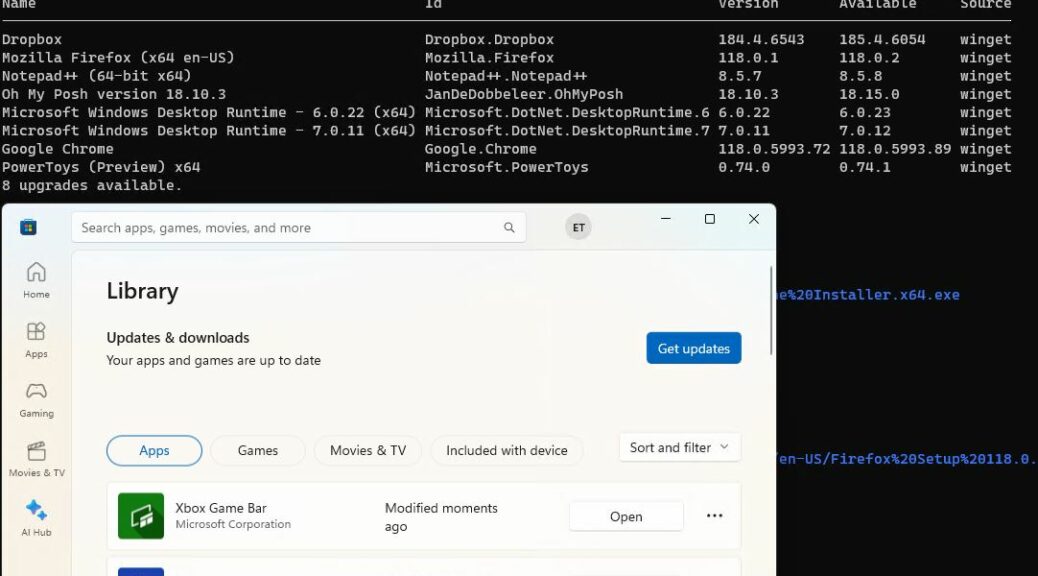
The lead-in graphic shows an artfully arranged update view of MS Store’s Library tab, with three items “modified momens ago” in front. Behind, you see winget inside Windows Terminal/PowerShell working to install 8 different updates.
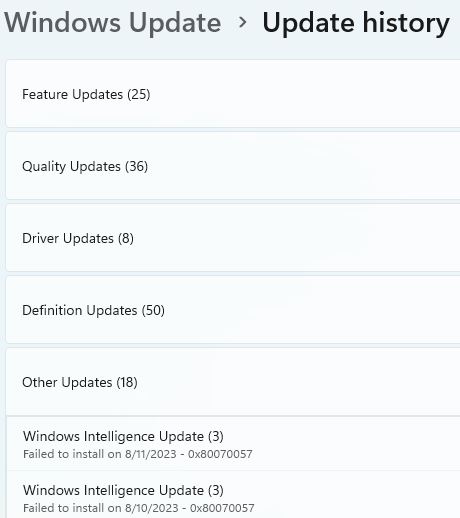
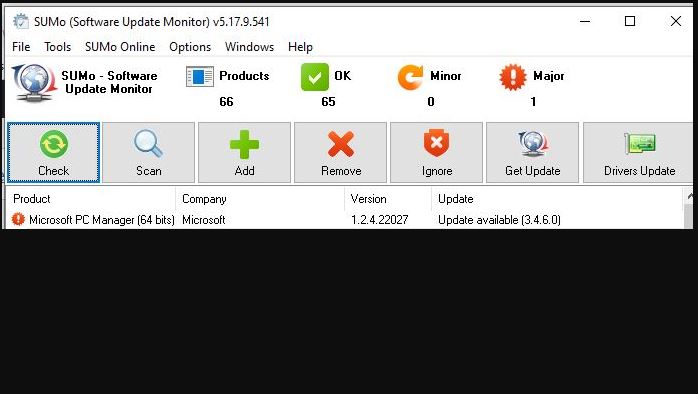
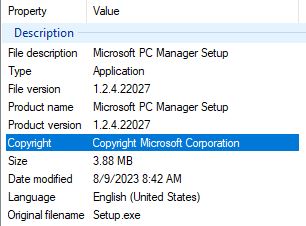
The amount of effort involved is pretty negligible, and the results are almost always trouble-free, speedy and reliable. Although I still have to turn to third-party tools to catch updates outside this ecosystem, under its umbrella things work pretty darn well.
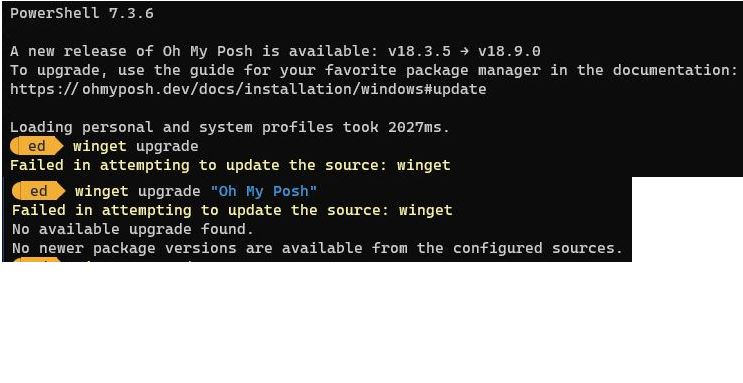
Now, if only those other app makers would get on the manifest circuit and start offering packages for winget to use, life would be entirely peachy. But alas, life isn’t like that — especially here in Windows-World, where a certain amount of chasing one’s own tail is too often a necessary part of the daily grind.
But a WIMVP can always hope for a better future, right? Surely, someday it will all be completely automated and totally easy. Yeah, right: I’ll keep dreaming about it, but that’s the closest I’m sure I’ll ever get.