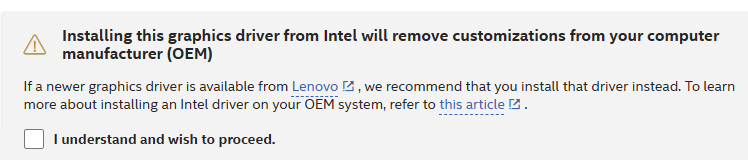
I’ll admit it: I’m a cheapskate. Case in point: both of my 5800X PCs still run NVIDIA GeForce 1070Ti GPUs, scavenged from long-retired older builds. Reason: the Antec 200 cases in which they resided couldn’t accommodate the longer, newer cards available at the time. In a surprisingly cryptic “Deprecation Schedule” document, however, NVIDIA reveals that GeForce 1070Ti nears EOL. In fact, the 580 series of drivers will be the last to support Maxwell, Pascal and Volta architectures. The 1070Ti was one of the last Pascal-era devices to go to market, so its days are officially numbered. The brief announcement that seals its fate appears as the lead-in graphic. Sigh.
If GeForce 1070Ti Nears EOL, What’s Next?
Looks like I’ve gotta buy two new GPUs for my pair of 5800X systems. Copilot recommends the NVIDIA RTX 4060 Ti as a logical replacment. It still works with the same 8-pin power connector, costs US$450-500, and is supposed to be 20-30% faster. For about the same money, however, AMD RX 7700 XT costs the same but offers a 10% performance bump. I’ll have to ponder those diffs and do some competitive shopping analysis.
That said, the last 58x driver drops in October of this year, concident with EOS for Windows 10. But Copilot says NVIDIA will offer security-only updates for another two years after that (until October 2028). So maybe I don’t have to hurry too fast to make that switch. After all, procrastination is my middle name here in Windows-World when it comes to spending money on enforced updates.
But as the technology base keeps changing, and my hardware keeps aging (along with your humble author, who no longer even qualifies as a “summer chicken”), switchovers are inevitable. I hope to hang out here in Windows-World enough longer to survive a couple more major technology turnovers. We’ll see!