I had the good fortune to provide copy edit and feedback to an MS person who works with Windows 10 recovery tools recently. From the blog post involved in our back-and-forth, I learned that two commands boot into WinRE (that is, the Windows Recovery Environment). Of course, a restart is required to make this happen. It’s not like Advanced Startup in Settings → Update & Security → Recovery → Advanced Startup. That is, you won’t immediately restart your PC as you do when clicking its “Restart now” button. I almost fell over when I tried that out for the first time!
Which Two Commands Boot Into WinRE?
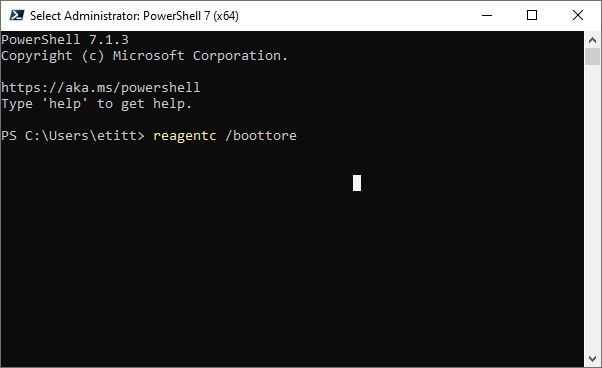
One I already knew about, the other is a welcome and interesting surprise. The surprising one uses a special switch for the Windows RE configuration tool — namely REAgentC. Turns out there’s a special option named “boottore” that does the trick. If you parse the string properly, it’s self-advertising: “boottore” = “Boot to R(ecovery )Environment.” Thus, that complete command is:
reagentc /boottore
The second one is a special version of the good old, familiar shutdown command. It takes two parameters–namely:
- /r Restarts the computer after shutdown
- /o Goes to Advanced boot options menu and restarts device, then boots into WinRE
Thus, the complete command is:
shutdown /r /o
What’re These Commands Good For?
Good question. In this modern era, transfer of control to the Windows loader often occurs extremely fast. This means that it can be difficult to impossible to interrupt the initial bootstrap process to divert over to an alternate boot menu — such as WinRE, BIOS/UEFI, boot device menus, and so forth. These commands put you in control over what happens after your next boot in advance. This has become my preferred method, because of the degree of control and guaranteed results that occur.
Shoot! Give one or both of them a try. You might come to like one or the other of them, too! For best results, run them in an administrative command prompt window or PowerShell session.