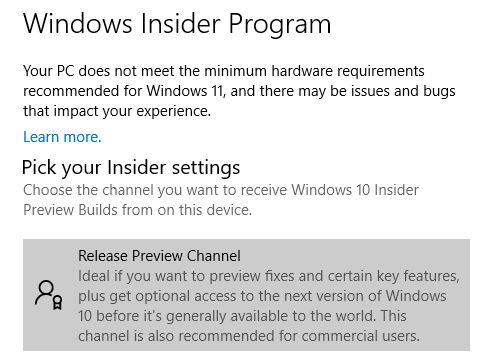
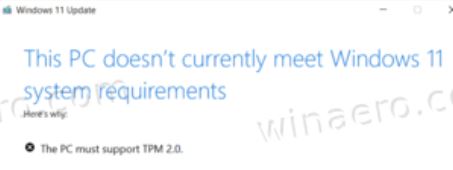
Until Windows 11 Build 22454 came along, the only way to get PowerToys was to download or update it from GitHub. But, as shown in the lead-in graphic for this story, the Windows 11 Store now offers PowerToys for download. Windows 10 users, however, will need to stick with GitHub going forward — at least for the time being. That’s what I gleaned from the WinAero story on this fork in the PowerToys development path.
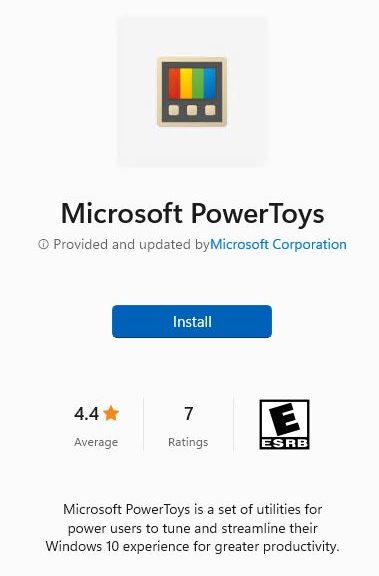
Visual Proof: Windows 11 Store Now Offers PowerToys
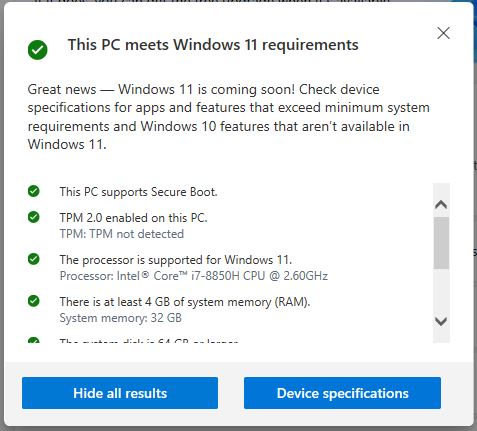
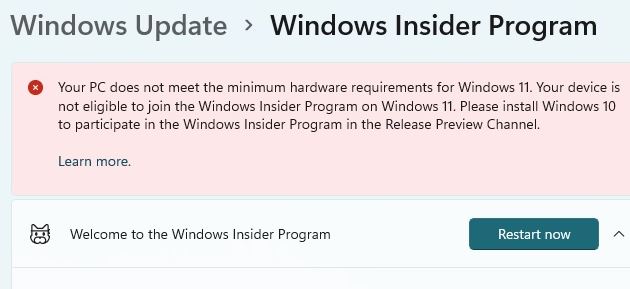
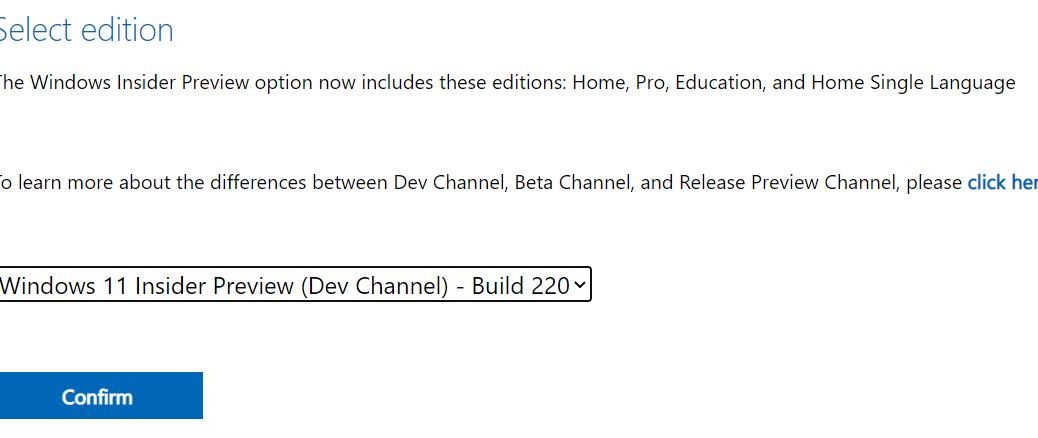
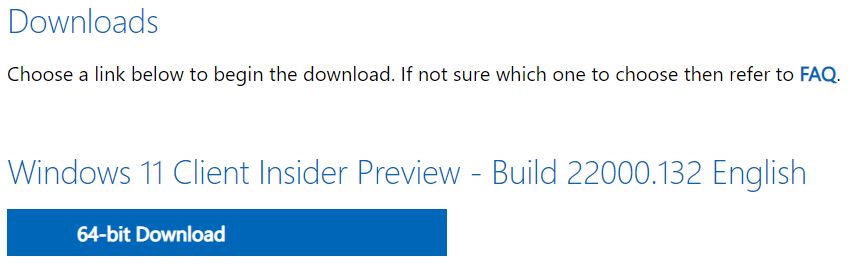
Because it’s available in the Store right now only to Windows 11 Build 22454 and higher, that restricts such access to Dev Channel Insiders. With the Beta Channel at Build 22000 at the moment, it could be some time before this pathway opens up to a broader segment of the Windows 11 population.
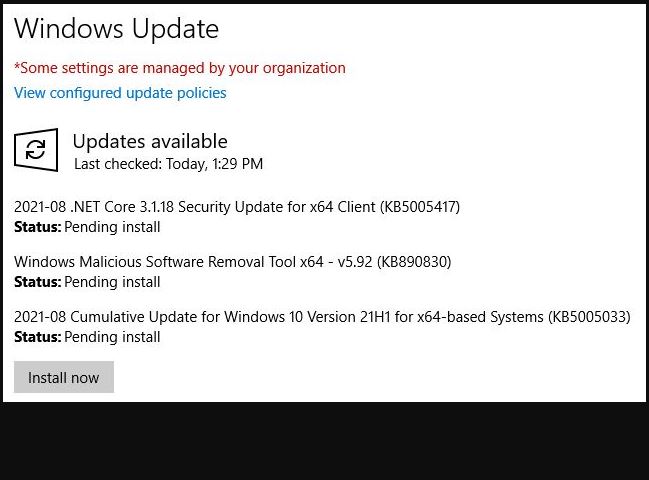
Being a “let’s try it and see what happens kind of guy” I checked the Store in the Beta version and searched on “PowerToys.” To my surprise, it came up there unhindered. It was absent, however, on Windows 10 when I tried the Store with the same search on my production PC (running Build 19043.1237).
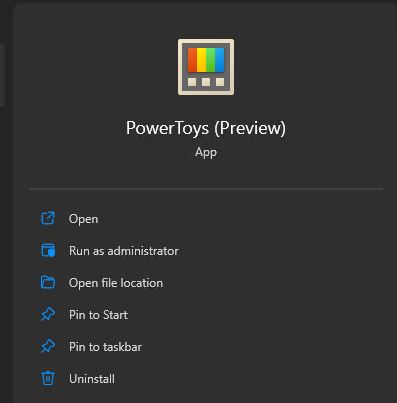
I clicked the “Install” button on the Beta channel PC (a Lenovo X380 Yoga Thinkpad model), and it reported a successful install. That said, I already had PowerToys installed on that machine, and it still comes up in the Start menu as PowerToys (Preview).
The (Preview) qualifier still shows up, which makes me wonder if anything really got installed.
So I uninstalled it, and then tried the Store-based install again. This time, it showed a download and I got a prompt asking if the installer could make changes to my device. The Installing progress circle continued until it said installed. And guess what: it still reads “PowerToys (Preview)” in its start menu listing. It did ask me to restart the tool as administrator, which tells me it is a new version (because I’d already made that change in its previous incarnation). I guess that means that PowerToys is getting ready for prime time, but has not yet reached production-ready status. That’s consistent with its 0.45.0 version number (a leading zero usually indicates something still in testing rather than production status).