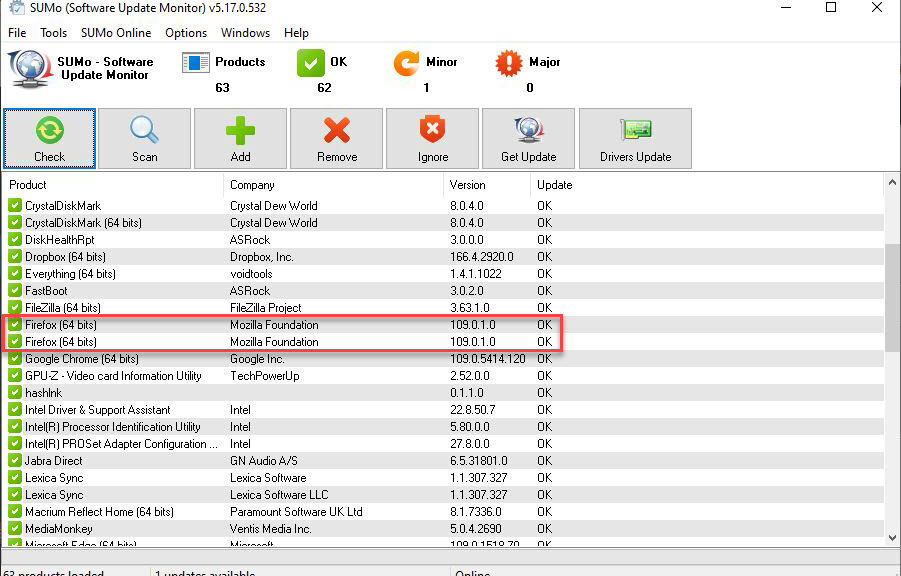
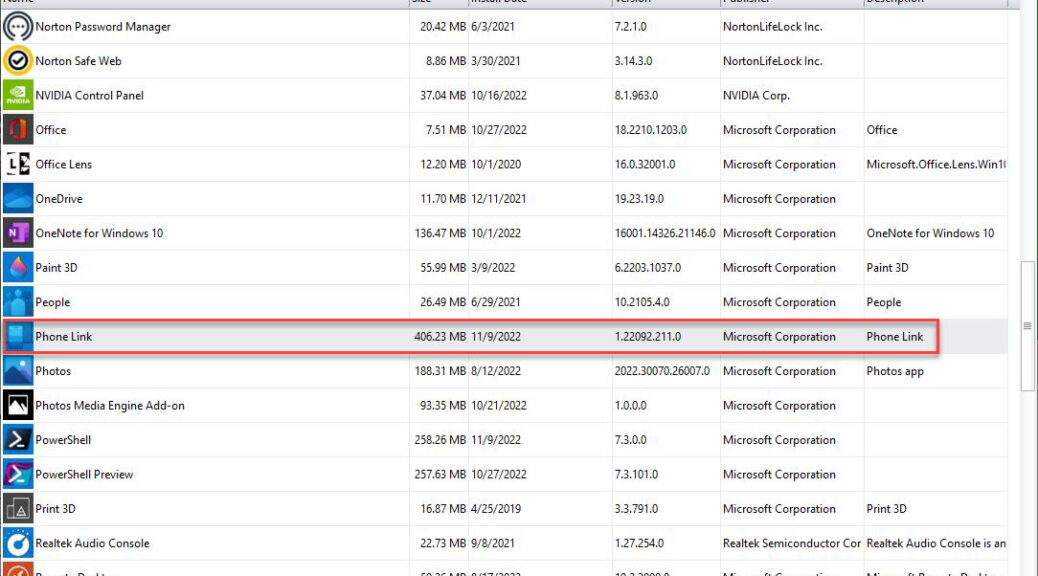
Oh boy! I just shot myself rather nicely in the foot but managed to call back the bullet. Let me explain, in the context of unfolding and frustrating Firefox x86 follies here at Chez Tittel. The lead-in graphic for this story shows two entries for Firefox as you can see in the red outline box. Therein hangs this particular tale…
Fixing Frustrating Firefox x86 Follies
I noticed this earlier this week when, after updating Firefox x64 on my production PC, I noticed a second copy still running the previous version. WTF? Using SUMO to show me the containing folders for each instance I saw what was up. One 64-bit copy is running in the Program Files folder tree. More interestingly, a second 64-bit copy is running in the Program Files (x86) folder tree. WTF again?
Nothing loath, I went into Explorer and deleted the Mozilla Firefox folder from the (x86) folder tree. This is the shooting myself in the foot part. Turns out that particular instance has all of my favorites, stored passwords, and yada yada yada. The true x64 instance is a “clean install” — but not in a good way. Sigh.
I called the bullet back by opening the Recycle Bin and restoring the entire, just-deleted Mozilla Firefox folder. I see that I can export all my stuff from one instance and then import it into the other. As soon as I have time to figure all that stuff out I can grab my “vital stats” from the x86 instance and make ready to transfer it into the x64 instance. Then, I should be able to safely delete the x86 instance without losing my valuable accreted data. Sigh again.
This Raises an Interesting Question…
What I really want to know is: how did an x64 instance of Firefox wind up in the x86 folder? I’m pretty sure that’s another self-inflicted wound. When I updated the trailing second instance earlier this week, whaddya bet it was a now-obsolete 32-bit instance for which only a 64-bit instance can serve as an update? Sigh one more time, and wonder why Firefox let me do this to myself. Go figure!
Alas, that’s the way things go for me sometimes in Windows-World. I’m just glad I was able to figure out and recover from my own foible without losing too much time or wasting too much effort.