Last August, Lenovo sent me a similar ThinkPad. Turns out, it was the Snapdragon X equivalent of what I’ve got now — namely, the ThinkPad T14s Gen 5. This time around, it comes equipped with an Intel Core Ultra 5 125U, 16 GB RAM LPDDR5 RAM, and a 0.5TB Gen4 NVMe SSD. It’s not quite as impressive as its Snapdragon counterpart, but it does come with an online price of just over US$1200 at the Lenovo Store. It showed up yesterday afternoon here at Chez Tittel. Here, I’ll share info about the Think T14s Gen 5 intake & first impressions. TLDR summary: nifty little biz laptop.
Detailing ThinkPad T14s Gen 5 Intake & First Impressions
It’s still a thrill to unbox new Lenovo computers these days, thanks to their all-paper packages designed for quick, easy access. The first thing I noticed was the boot time (after I plugged the 65W USB-C charger in: the unit was at 0% charge). On first boot, it takes less than 10 seconds to get from power on to spinning balls (Task Manager reports “Last BIOS time” at 11.4 second), and less than 10 seconds more to get to the desktop. Closing the lid puts the unit immediately to sleep, and it takes less than 4 seconds to scan me with its IR Windows Hello camera and log me back in when I open it. Good-oh!
My recollection is that the Snapdragon X model was a little bit faster than this Intel Core Ultra 5 125U CPU. That said, the unit is pretty darn snappy, and does everything I ask it to do with verve and dispatch. CrystalDiskMark reports top speeds of ~7 GBps read/~5GBps write from its capable Gen5 SK Hynix SSD (random 4K r/w performance is 409/334 [QD32] and 65/129 [QD1] MBps). That’s on par with my beefiest test laptop — the big and beastly P16 Gen 1 Mobile Workstation.
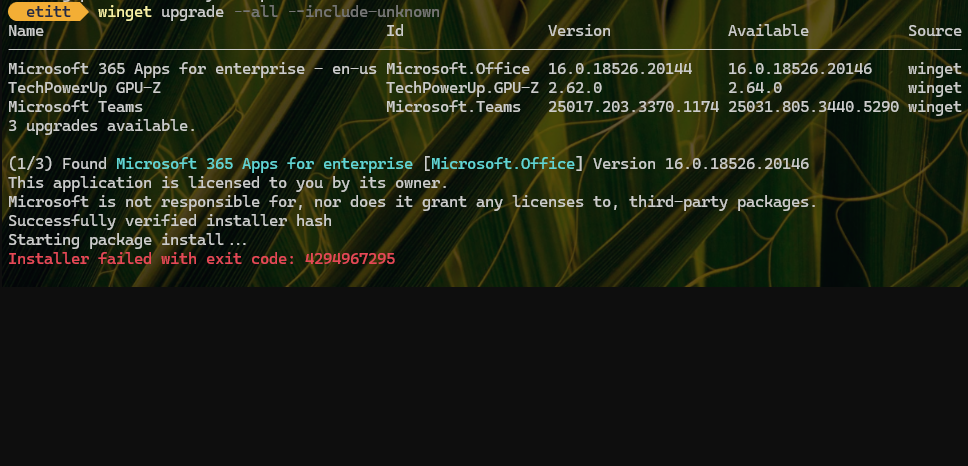
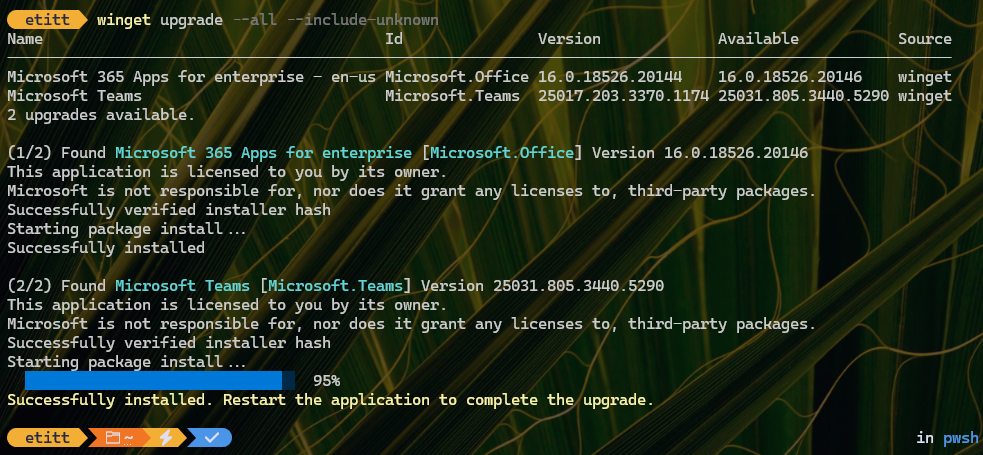
I used PatchMyPC Home Updater to get most of my typical collection of tools and apps installed. The T14s did a nice job throughout, and the whole process took less than 20 minutes to complete. Then, I went to update Windows 11 24H2, as I’ll recite under the next heading…
Updating Windows 11 24H2 Takes Time
For some odd reason, WU installed a boatload of stuff when I did my usual “first boot” update check — 2 CUs, 23 drivers, the most recent MSRT, and various Defender updates (signatures and platform). This took long enough that it reminded me of pre Windows-7 days when installing Windows took nowhere near as long as catching up the OS image on updates after that first step was over. This was unusual, but not unheard of.
And now, I’ve got this nifty little unit ready to rock’n’roll for further inspection, testing and use. I’m glad to have it because I want to compare OTA Ethernet and GbE network file transfer to Intel’s Thunderbolt Share application. This PC gives me my vital “second Thunderbolt 4 PC” so I can check that out. Stay tuned!






![Pondering Intel Core Ultra Series 2 CPU Strategies [Image source: intel]](http://www.edtittel.com/wp-content/uploads/2025/03/intlcorultra-1038x576.png)
