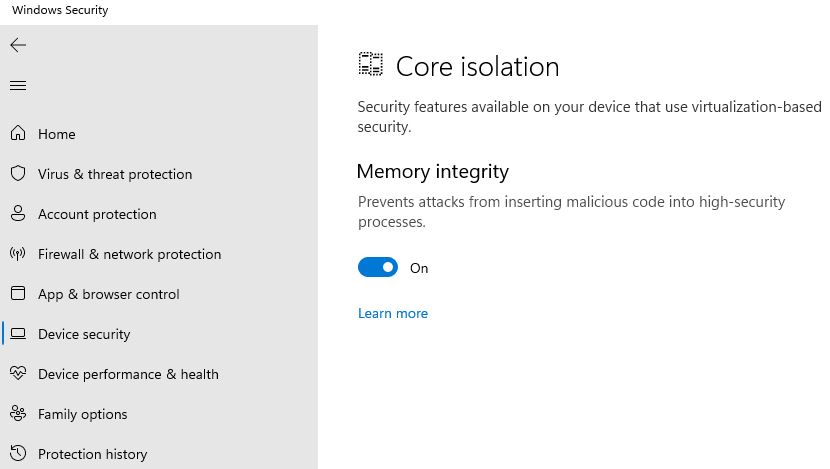
With the latest versions of Windows 10 and 11, Windows Security gains driver level protection. I’m talking about Build 19044.1586 or higher for Windows 10. Also, 22000.593 or higher for production 11, and 22581.200 or higher for Dev Channel Insider Previews. Looks like those still running Beta (22000.588, or higher) are also covered. Go into Microsoft Security, under the left-panel Device security heading. Drill into Core isolation details, then turn on Memory integrity (see lead-in graphic). Do all those things, and Windows memory integrity now covers device drivers. I’ll explain. . .
What Windows Memory Integrity Now Covers Device Drivers Means
With Core Isolation turned on (requires Hyper-V and VM support turned on in UEFI or BIOS), you can visit the MS Support Core isolation page to learn more. It also provides detailed, step-by-step instructions on how to turn this feature on (note: a restart is required).
Here’s a brief summary:
1. Memory integrity, aka Hypervisor-protected Code Integrity (HVCI), enables low-level Windows security and protects against driver hijack attacks.
2. Memory integrity creates an isolated environment (e.g. a sandbox) using hardware virtualization.
3. Programs must pass code to memory integrity inside the sandbox for verification. It only runs if the memory integrity check confirms code safety. MS asserts “Typically, this happens very quickly.”
Essentially, memory integrity/core isolation puts security inside a more secure area. There it can better protect itself from attack, while prevents drivers (and the runtime environments they serve) from malicious code and instructions.
What Can Go Wrong?
If any suspect drivers are already present on a target system, you can’t turn memory integrity on. Instead you’ll get an error message something like this:
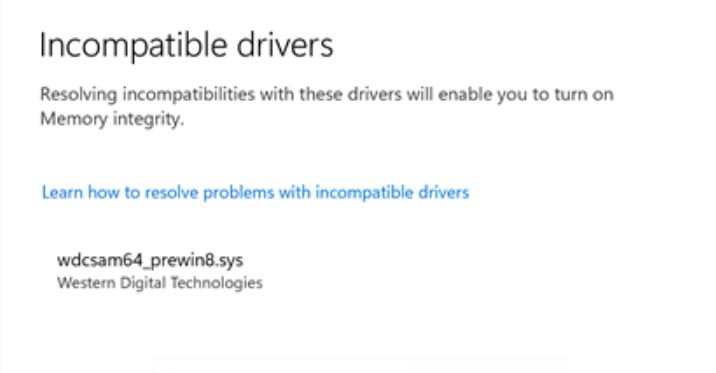 Note: the name of the driver appears in the warning. Thus, you can use a tool like RAPR.exe to excise it from your system. Be sure to find and be ready to install a safe replacement because that may render the affected device inaccessible and/or unusable.
Note: the name of the driver appears in the warning. Thus, you can use a tool like RAPR.exe to excise it from your system. Be sure to find and be ready to install a safe replacement because that may render the affected device inaccessible and/or unusable.
Should you attempt to install a suspect or known malicious driver after turning this security feature on, Windows will refuse. It will provide a similar error message to report that the driver is blocked because it might install malware or otherwise compromise your PC.
That’s good: because that means driver protection is working as intended. Cheers!