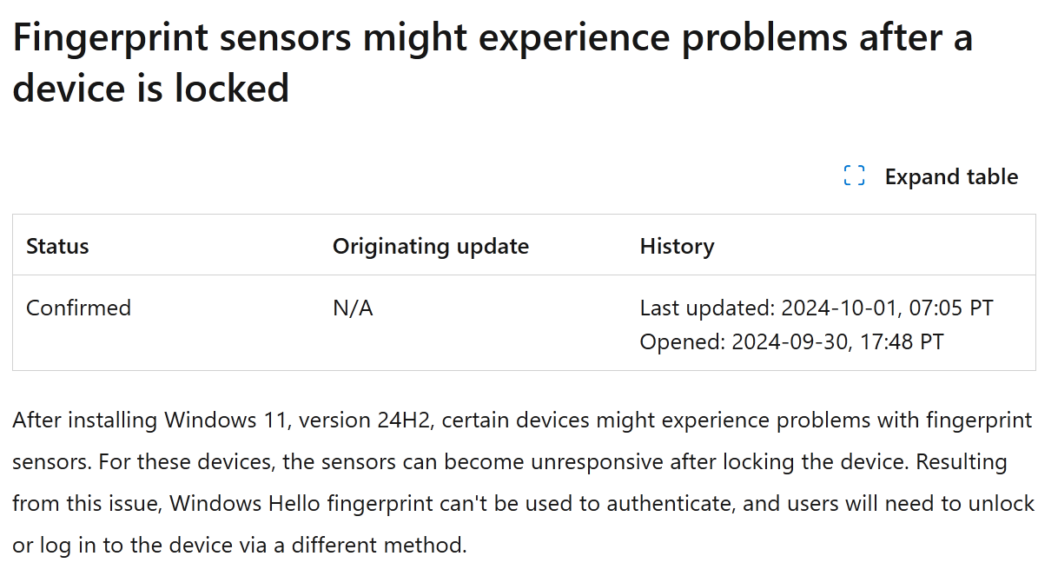
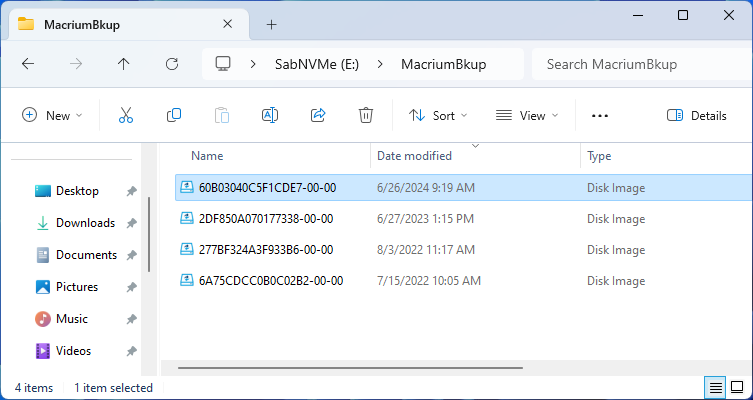
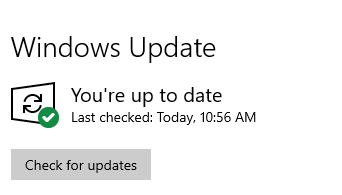
I’m getting down to the bitter end, and it’s troubling me. The Lenovo ThinkPad X1 Extreme still gets no 24H2 offer from Windows Update. Indeed, it’s my only remaining 23H2 holdout. Looking at the 24H2 Known Issues List, I can’t figure out why. One outstanding possibility is the Synaptics WBDI fingerprint reader. But shoot, it’s dated 12/4/2022. I’m puzzled… OTOH, Copilot says that Intel Display Audio drivers include Intel SST audio support, and that’s a listed issue as well. It could be the blocker, and a good thing to know.
Waiting Impatiently, as X1 Extreme Still Gets No 24H2 Offer
Here’s what I’ve done to try to address potential update hold issues:
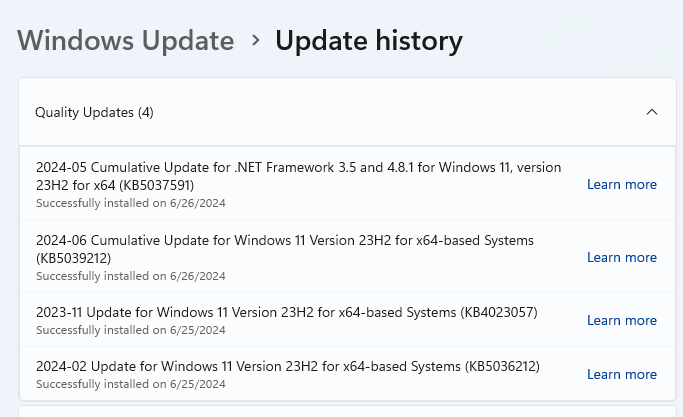
- Applied all Optional updates, including drivers
- Use Snappy Driver Installer Origin (SDIO) to update NVIDIA and Intel Display Audio drivers (restart required)
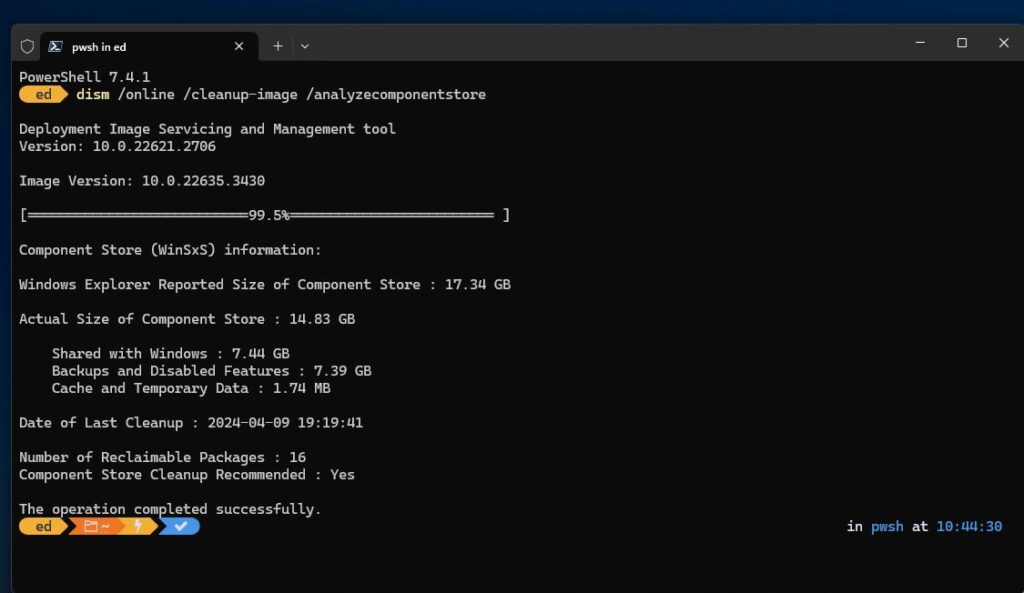
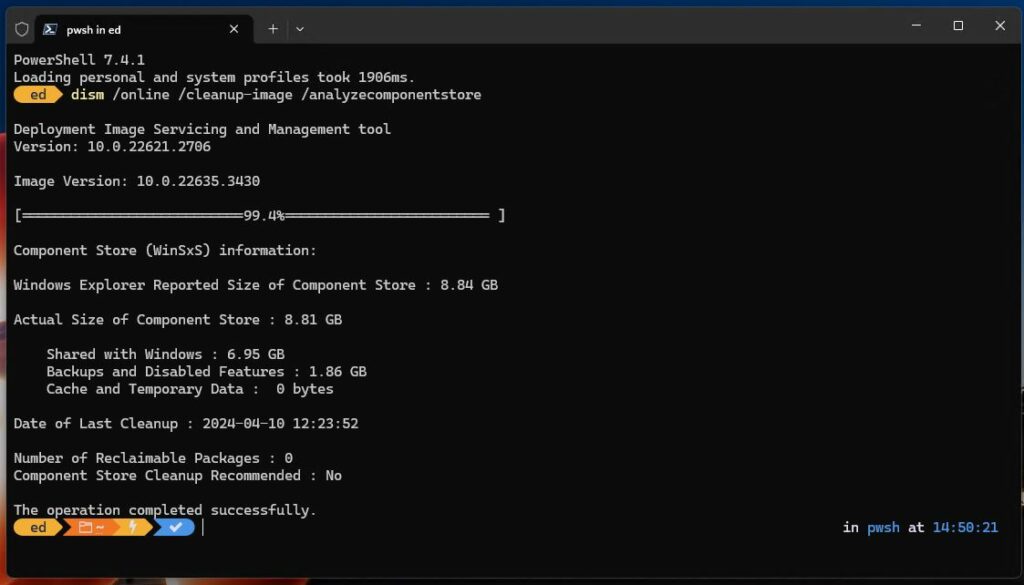
- Run comprehensive cleanup and integrity checks (PC Manager, DISM, sfc, etc.)
Still no joy, and no real clue on how to get over this hump. All in all, I’m both miffed and bemused that a 2018 vintage (8th-Gen) i7 PC is still lagging behind the update pack. I’m biting my tongue, holding back on forcing matters. I guess I have a perverse desire to see how long it’s going to take for WU to come through with 24H2.
Only time will tell, I guess! And that’s they way things go sometimes, here in Windows -World.
Additional Oddments Present on X1 Extreme
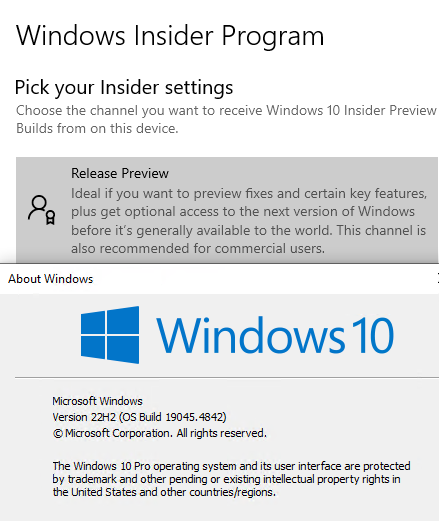
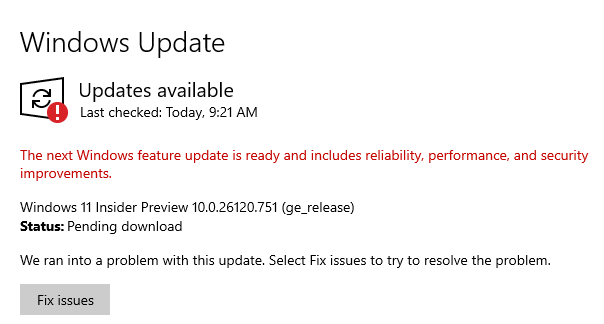
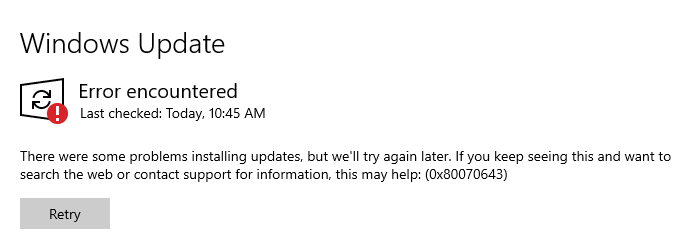
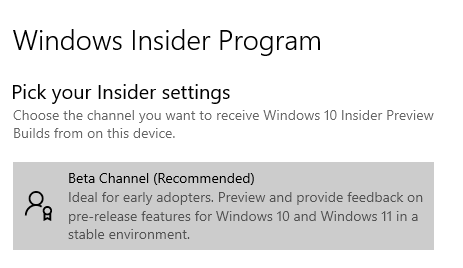
OK, so today is Patch Tuesday. I couldn’t get WU to present KB5046633, so I downloaded the self-installing update file (.msu). It took nearly an hour to get it up and going again, but the PC is now running 22635.4460. I suddenly understand that this PC is running the Beta Insider version (a surprise to me, or perhaps a “senior moment”). THAT explains why the update took so long: it had LOTS of work to do to fit it into the beta release…
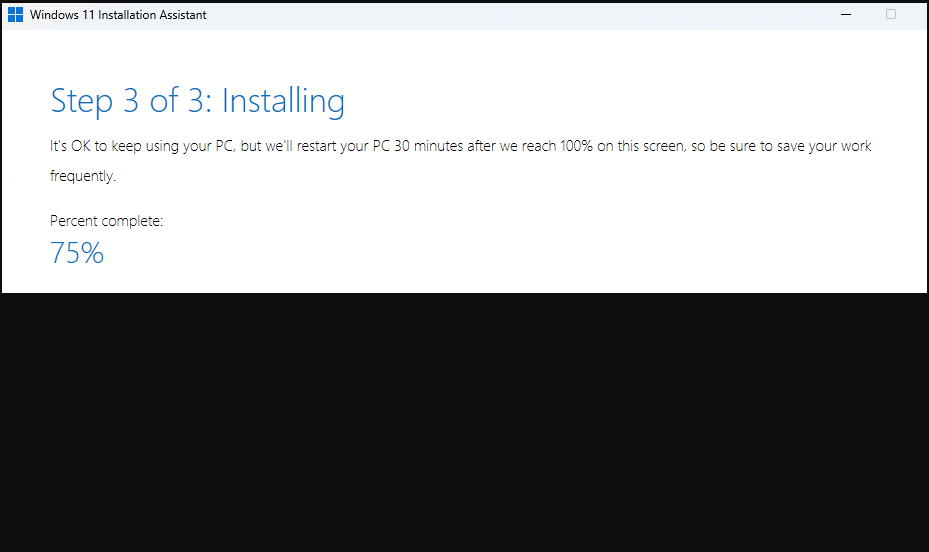
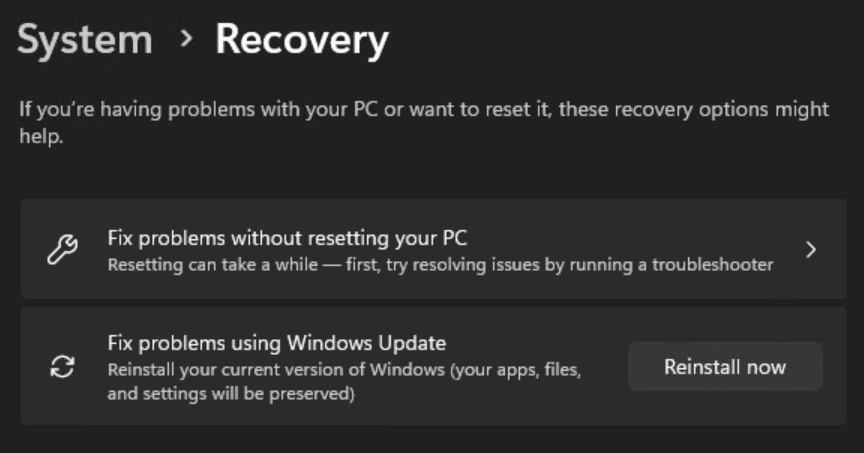
Given that it’s running an Insider version anyway, I’ve decided to force matters using the 24H2 Installation Assistant. Here goes… Chunking through the GUI portion without issues, but took awhile (~ 45 minutes). First reboot to completion: same again. But I had no idea the Windows Installer could play such hopscotch with Insider Preview updates. I just flat thought it wouldn’t work. It’s actually kind of amazing. And, with many things in my Windows experience, the biggest surprises — like this one — are mostly self-inflicted.
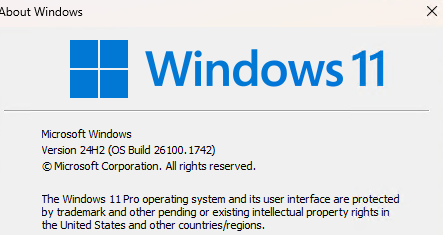
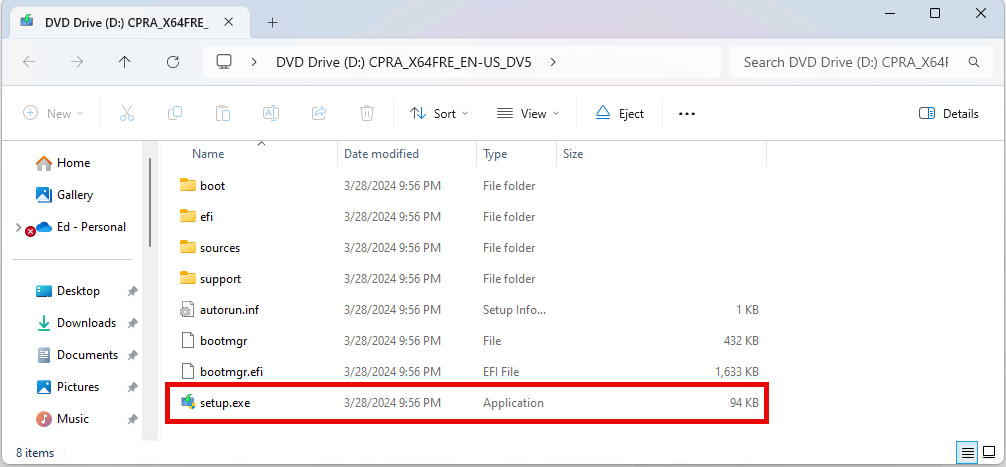
There is a problem though: the Build Number currently self-reports at 26100.1742. This corresponds to the early October build for plain-vanilla 24H2, NOT the beta version. I just ran WU and updated again, and it still reports the same build number. Very strange! I’m going to build an ISO for 22100.2314 and see if it will repair install. This is getting decidedly interesting…