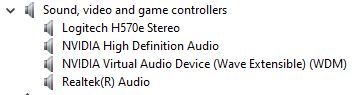
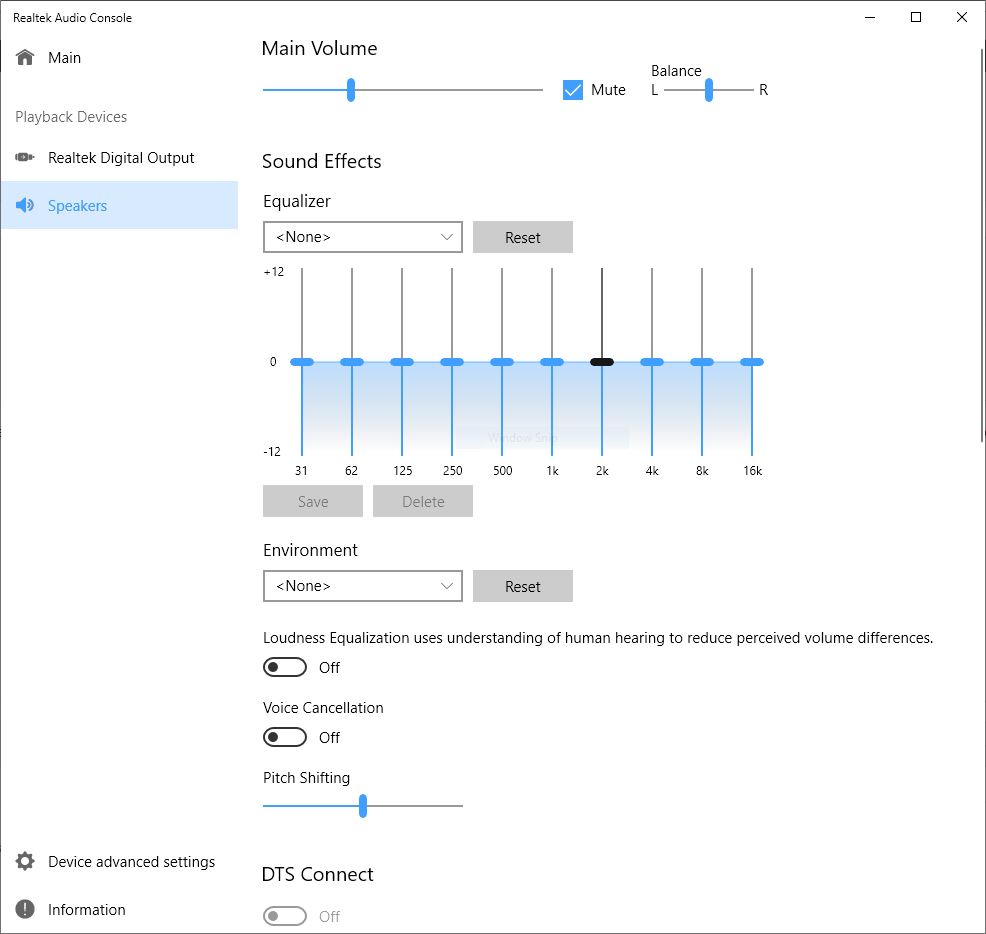
I’ve learned the hard way that working with Realtek Universal Audio Driver (UAD) drivers can be interesting. I’ve accidentally switched back from the “Realtek(R) Audio” drivers shown in first screencap for this story to the Realtek HD Audio drivers more than once. But alas, only the “Realtek (R) Audio” drivers work with the Realtek Audio Console UWP app (see next image following). That’s why I wrote today’s post on the topic of updating Realtek UAD Audio Drivers. There are several steps involved, and a couple of (usually reliable) sources to which I turn for driver downloads. Read on for those details please!
The name of the driver says nothing about UAD. You must simply recognize that the name “Realtek (R) Audio” signifies that a UAD driver is present and running.
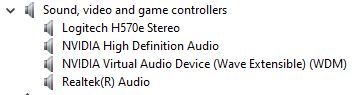
Simply put, one MUST install the UAD (Realtek(R)) driver to use this UWP app.
[Click image for full-sized view.]
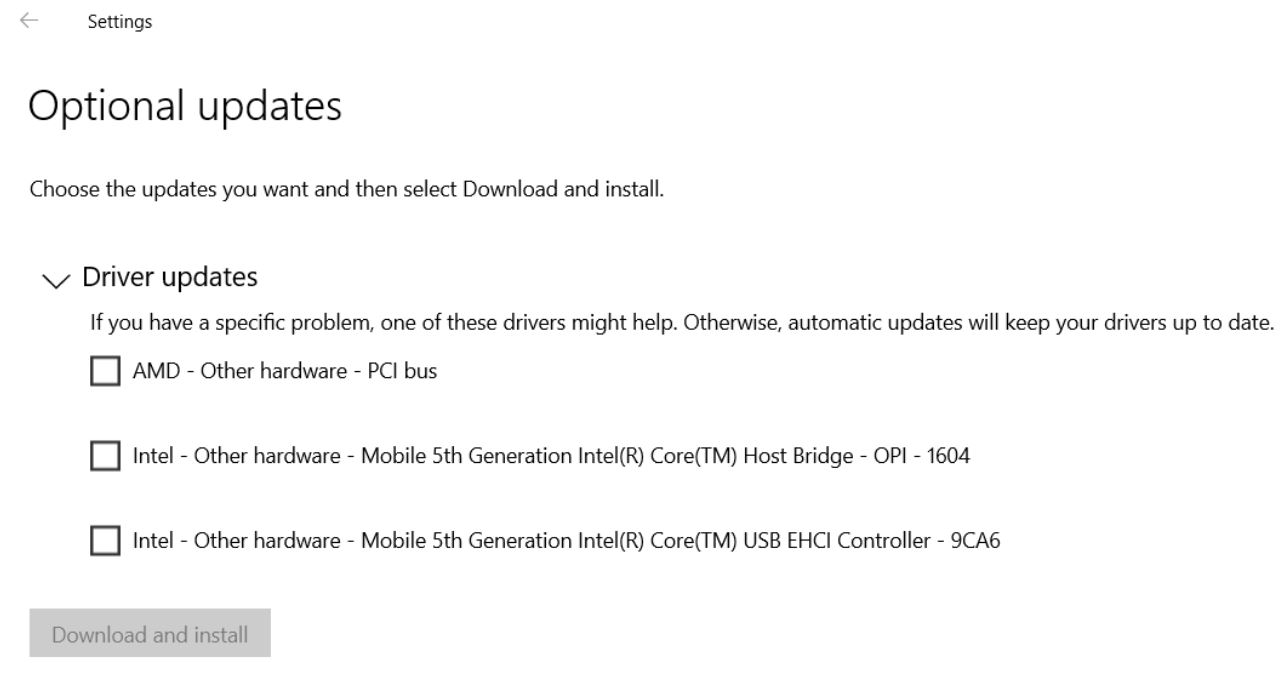
Updating Realtek UAD Audio Drivers 1: The UAD Driver Itself
I use the excellent French Station-Drivers website to grab my UAD drivers. There, Realtek Audio gets its own landing page. It’s still a bit of a slog to get to the right driver from there. I’ll explain this as a sequence of steps for my particular motherboard, which comes from Asrock:
1. Click on Realtek High Definition Audio (HDA/UAD)
2. Click on Drivers (UAD).
3. Click on the name of your motherboard (or system) maker. (In my case, that’s Asrock.)
4. Examine the listings to find the highest-numbered drivers version (at bottom of list; in my case, that’s 8890.1).
5. Click on that version link, then click “Download” on the resulting web page.
This will grab a ZIP file that you can use to unpack and install the driver. Personally, I prefer to right-click the driver inside Device Manager, and point the “Update driver” option at the folder location where I unzipped the download file contents. Why? Because the Realtek installer requires not one, but two (2!), reboots to do its thing. I can use my right-click technique to update the driver without rebooting at all. Do what you like best on your PC(s), though.
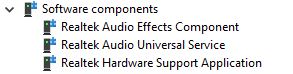
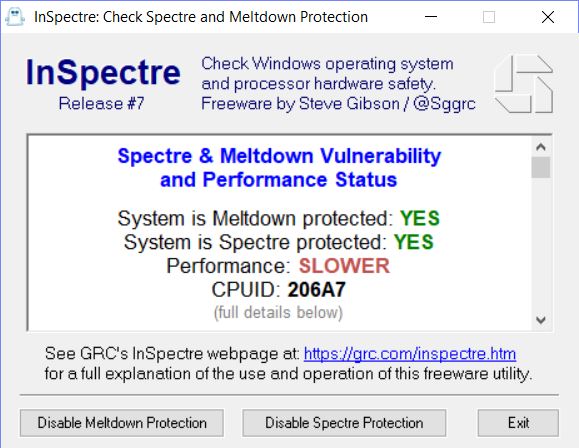
Updating Realtek UAD Drivers 2: The Software Components
If you open the category in Device Manager named Software Components, you should see something like the next screencap, which shows three (3) additional Realtek software components. You can update the first two of these three items. I grab them from DriverHub, by searching for them by name. That is, I search on “Realtek Audio Effects Component” and “Realtek Audio Universal Service” and download the corresponding ZIP files. Right-clicking those drivers in Device Manager, to point the driver update function at the contents of those ZIP files works fine to update them, too.
Only the first two of these three drivers get updates, for whatever reason. Thus, that’s all you need look for.
I do this once every six months or so, unless I see a news or other online info item (perhaps at TenForums, which I visit more or less daily) to tell me an update is available sooner. And that’s how I keep my Realtek UAD audio driver and supporting items up-to-date!