In reading through my usual Windows news and info sources this morning I came across a scary notification at MS Power User. The named item is from the national vulnerability database. CVE-2024-6738 — which makes it item 6,738 for 2024 — comes with scary implications. It’s been reported in some form since last February. It attacks by altering meta-data for Windows base log files (BLFs) and can cause doom loops like those recently experienced from a Crowdstrike update last month. Thus, CVE-2024-6768 exposes scary Windows vulnerability that is hard to fend off and tricky to repair.
BLF Alteration in CVE-2024-6768 Exposes Scary Windows Vulnerability
A base log file (BLF) sits at the heart of the Windows Common Log File System (aka CLFS). As MS Learn’s “Creating a Log File” article begins, it says:
Before you can use CLFS, you must create a log file using the CreateLogFile function. A log file is made up of a base log file that contains metadata, and a number of containers that hold the actual data. On any local file system, containers can be in one or more separate files; on NTFS, containers can be in one or more streams within a file.
The BLF contains key information that describes the associated containers for log data. If the BLF is wrong, the log won’t make sense and cannot be read. This doesn’t sound like a big deal, but it is. Let me explain further…
Several Interesting Copilot Responses…
When asked to describe BLF files, Copilot notes how they’re used:
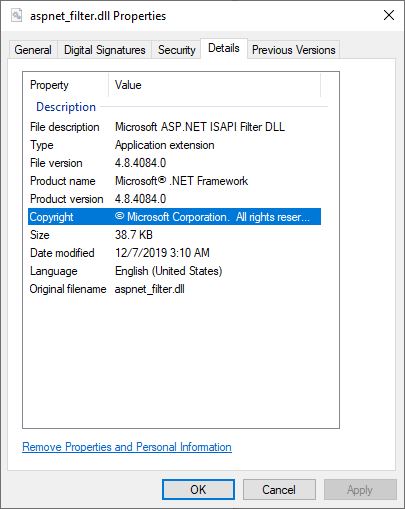
Usage: These files are crucial for maintaining system stability and integrity. They help manage user-level registry information and other system-level data. For example, the Windows component that writes user-level registry information to the
NTUSER.DATfile uses CLFS logging, which involves BLF files1.
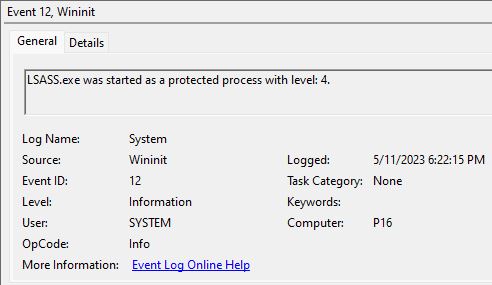
Indeed it seems that CVE-2024-6768 wreaks havoc by breaking the base log handler with a bogus “size of data field” value. This kind of error triggers a BugCheck error, and in turn provokes a BSOD.
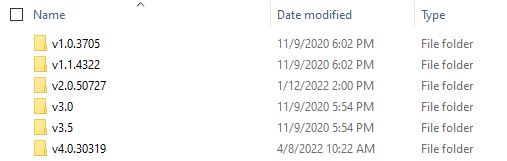
Further investigation shows that any time a registry change occurs BLF files get updated. They are also essential to system boot-up, application installation and update, as well as system update. To get more details ask Copilot: “When do Windows base log files get written, and when do they get read?” You’ll see what I mean right away.
What Does the Future Hold?
The Fortra release note for this vulnerability shows its history, while a companion research note shows more details. So far, MS has yet to respond. Other than research work, I see no evidence of successful exploits in the wild. That said, this kind of attack is nearly impossible to fix without knowing the exact details of the registry values changed to mung some (or more) specific .BLF file(s).
IMO, this means the only real protection is a recent image backup that will replace the altered Windows image with a known, good working copy. Stuff like this is why I keep such things handy, and make one at least daily. This could get interesting…stay tuned!