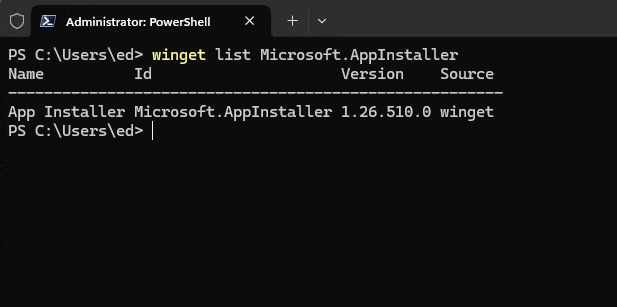
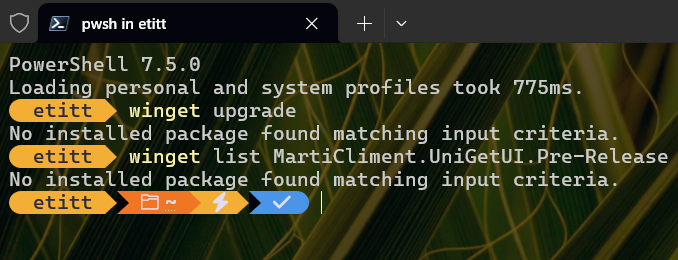
Late last April, I wrestled with getting winget updates (aka Microsoft.AppInstaller) to “take.” That is, figuring out how to follow the advice to “restart the application” so the new version could take over. Turns out that nothing short of a restart seemed to guarantee that the update would run in PowerShell/Windows Terminal. Other techniques — killing all active processes, open/close WinTerm, and so forth — did not always suffice. A recent Winget update re-raises restart requirement, as I tried to move from version 1.26.430.0 to 1.26.510.0. It was the same darn thing all over again!
Why Winget Update Re-Raises Restart Requirement
If you read into my April blog post that offered explanations from two winget mavens, you’ll see that the winget upgrade waits until dangling APIs and runtime modules, plus pending package updates, all get resolved before completing its own upward move. For the chronically impatient — including yours truly — that makes a restart/reboot a surefire way to FORCE the changes through as a consequence of shutting down, then starting back up.
It worked last April, and it still works now. But a restart on my production PC with its numerous peripherals and 6 drives showing in File Explorer, is no small thing. It takes over a minute to shut down, and another 2-3 minutes to get through restart and to the desktop. So while it does the job, it also makes me wait rather longer than I’d really like to.
But hey: that’s the way things go in Windows-World sometimes. When things change, waiting for “out with the old, in with the new” can take some time. Maybe I should go get another cup of coffee…