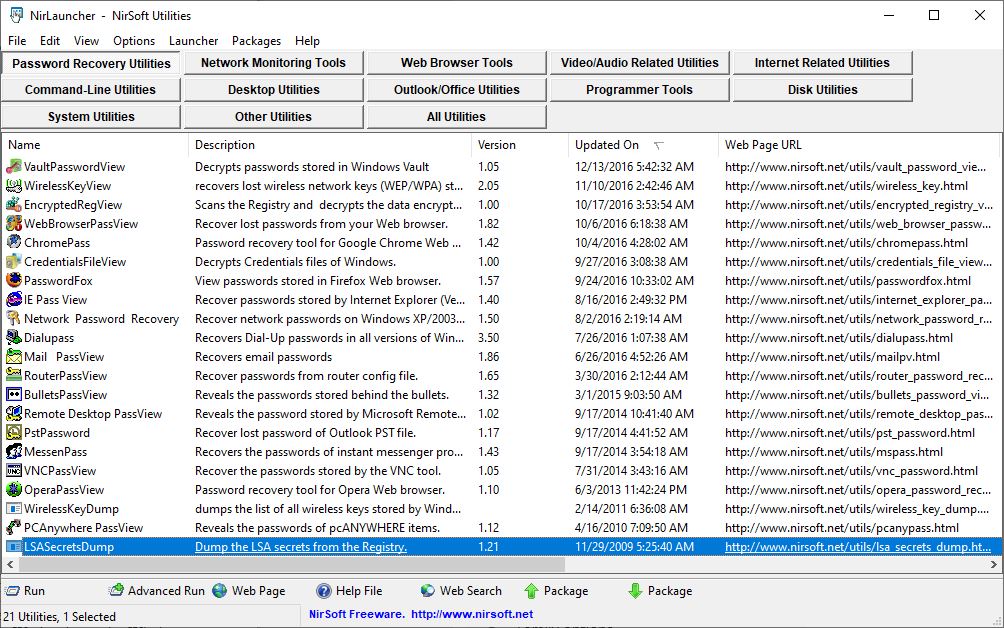
The other day, I had Windows Defender scan all of my disk drives. This action artificially provoked a performance alert on one of my Lenovo laptops. While it was running it reported 8 malware items on my D: (Data) drive. Please note: all of these are categorized as “HackTool” items. MS correlates them with specific malware items and known exploits. After overcoming my initial alarm, I looked where those items were found. All resided under parent directory D:\NirLauncher. Immediately, certain things became clear. Every one of the suspect elements is a password sniffing and capture tool in Nir Sofer’s collection of Windows Utilities. In fact, he’s got a category within that collection of 200-plus tools called “Password Recovery Utilities,” which comprises 20 items (see below). All of them popped up here. Aha!
Once it found these items, Defender forced me to have it ignore these threats to retain access to them.
[Click image for Full-Sized View.]
If Certain Legit Tools Generate Windows Defender False Positives, Then What?
Once Defender finds something suspect, you must remove that item from its clutches before you can use it again. That meant I had to open Windows Security → Virus & threat protection, then click on each item it found. Next, I clicked “See details,” and then explicitly told it to ignore each threat one at a time.
As you might expect, there’s a better way to deal with this kind of thing if you prepare in advance. If you click “Manage settings” inside the Virus & Threat protection pane, you’ll find an Exclusions setting right below Controlled folder access. Click “Add or remove exclusions” and you can instruct Defender to bypass specific files or folders. I simply added an exclusion for the D:\NirLauncher folder and it will now be ignored in future complete system scans (the Quick Scan option only accesses the Windows C: drive anyway).
Pre-emption Beats Reaction Whenever Possible
Currently, I use several utilities that Defender flags as threats. In addition to NirSoft’s password utilities (which NirLauncher includes amidst its collection of tools), I’ve had to exclude Gabe Topala’s System Information for Windows (siw.exe). In days of yore, before I started using Superfly’s ShowKeyPlus, I used a tool called Magic Jelly Bean Finder that likewise got flagged. I excluded it, too.
The moral of the story is this: if you’re planning to install (or copy standalone) tools that find passwords or keys, chances are pretty good that Defender will flag them as Hacktools. If you take steps to exclude them in advance, you can avoid having to “Ignore” them later on. But please: make sure you run any such software through VirusTotal to be doubly darn sure it’s safe before allowing it to take up residence on your PC. Such tools can indeed be used for malefic purposes, as well as legitimate ones. Be safe out there!