I ran into an interesting problem this weekend. The “Your credentials did not work” error appeared when I added my usual MS admin-level account to the Lenovo X390 Yoga. I checked all the usual suspects with no change in status. That means: remote access settings, account status, and so forth. Ultimately I had to search the error message via Google. And that, dear readers, is how I learned group policy edits fix broken RDP credentials.
How Group Policy Edits Fix Broken RDP Credentials
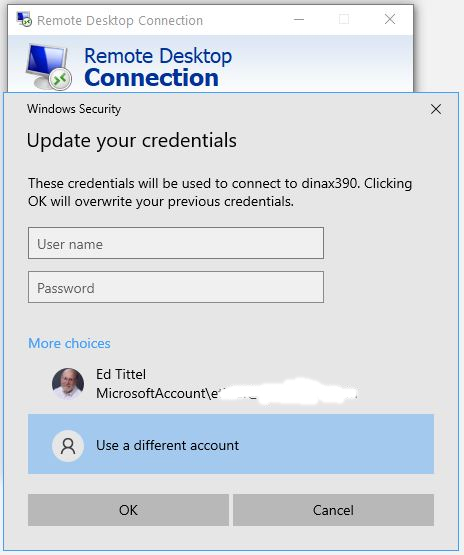
Even though I was using the same long-standing Microsoft Account I use for admin level login on all of my Windows 10 PCs, this one wouldn’t work. At one point, error messages informed me about a problem with LSASS (local security authority subsystem service, the OS component that handles logins). Later on, that error changed to “Your credentials did not work.” Sigh.
Because I had no trouble using the same account name and password (plus 2FA authentication through MS) to log into that PC locally, I knew the problem was focused on RDP. And indeed I turned up an extremely helpful article at Appuals.com. Entitled Fix: Your Credentials Did not Work in Remote Desktop, it let me to a working solution.
Group Policy Changes Needed
For me the items I had to enable, and then add the value TERMSRV/* resided in the edit path named
Computer Configuration > Administrative Templates > System > Credentials Delegation
Those items numbered 4, as follows:
1. Allow delegating default credentials with NTLM-only server authentication
2. Allow delegating default credentials
3. Allow delegating saved credentials
4. Allow delegating saved credentials with NTLM-only server authentication
Once I had made those changes, I had to restart the target PC. I also had to manually re-enter the credentials I’d attempted to use beforehand (without success). Then, finally: Boom! RDP accepted my connection attempt on the usual MS admin account. Problem solved. That was an odd one…