After my amazing experience in forcibly upgrading the Lenovo X12 hybrid tablet yesterday I’m pondering upgrade strategies. Indeed, 2004 and 20H2 Windows 10 PCs are in line for the 21H1 upgrade. But Microsoft’s criteria for offering that upgrade — and thus also, its timing — are unclear. Hence my question: “Is forcing Win10 upgrades good?” As is the case with most good questions, the answer starts with a predictable phrase: “That depends…”
Answering “Is Forcing Win10 Upgrades Good?”
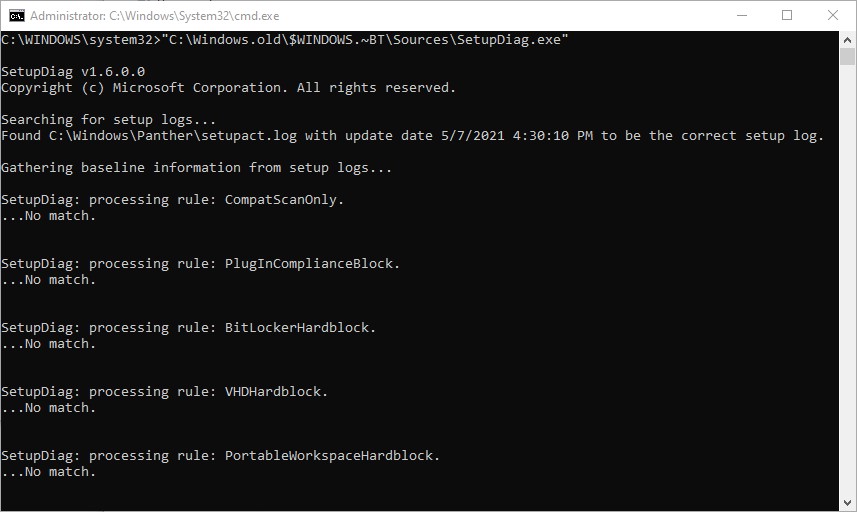
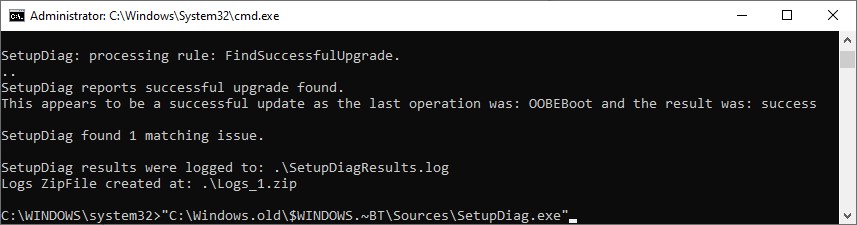
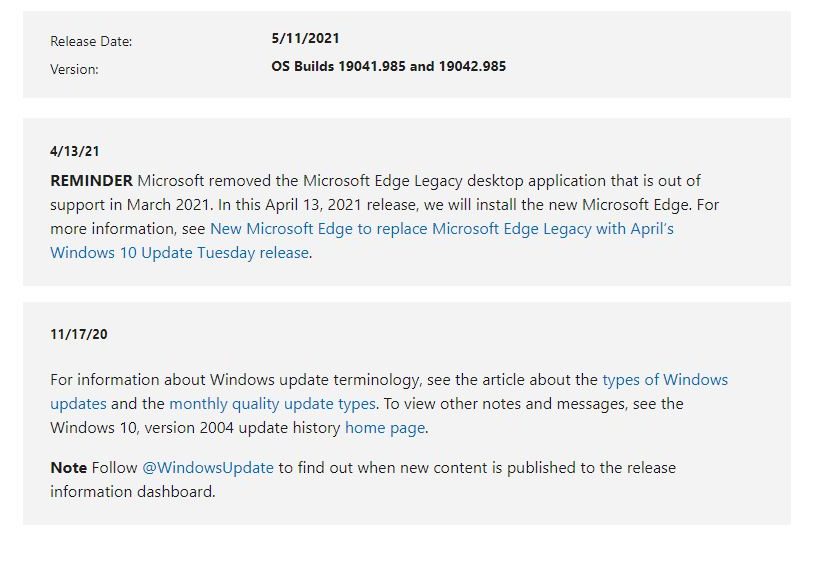
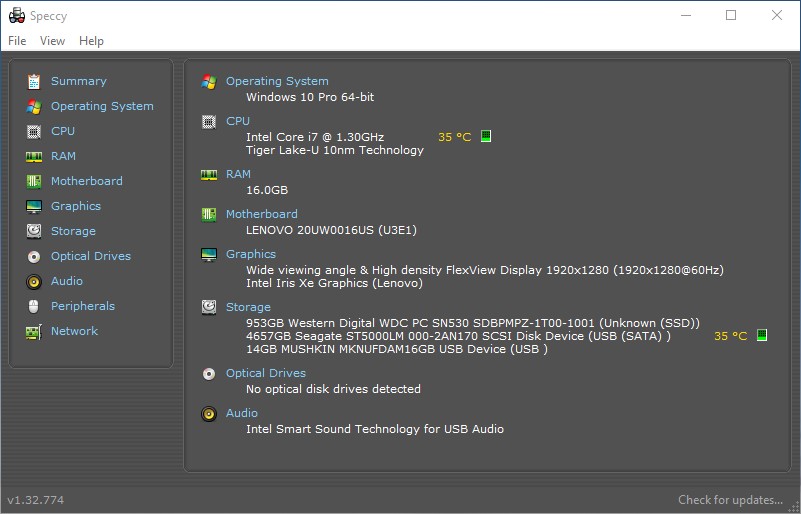
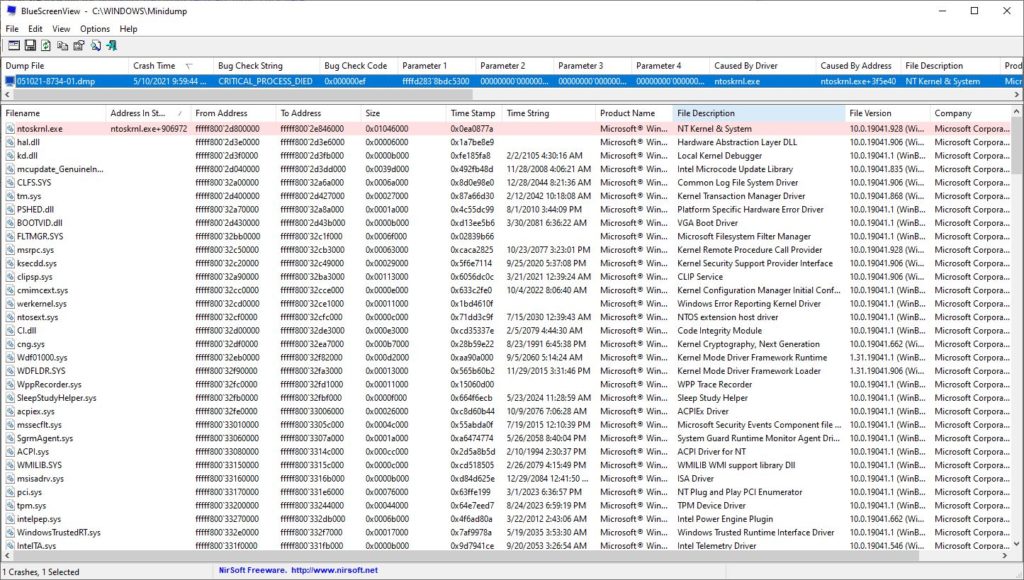
I got to 21H1 on the X12 by downloading a self-installing upgrade file (.MSU) from a link at TenForums.com. Here’s what that info looks like on that page (links are not live, and you’ll soon understand why):
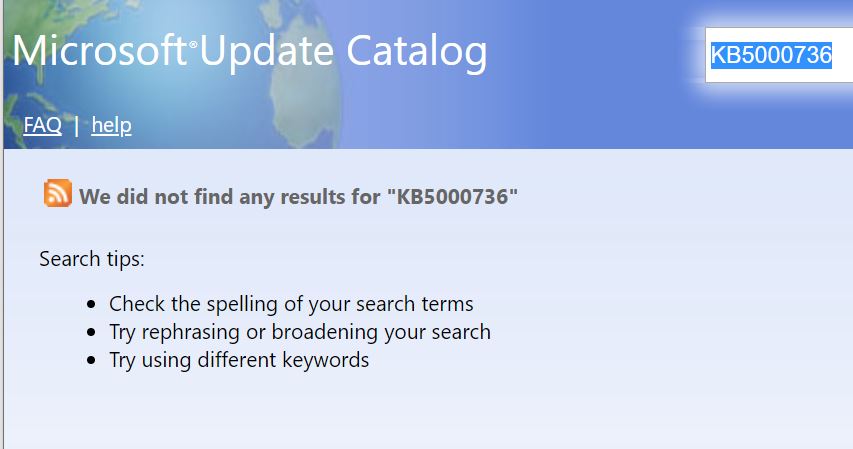
These catalog downloads no longer show up when you search the catalog, but they’re still live.
[Click image for full-sized view.]
Those links do work (I’ve checked) and they come from download.microsoft.com, which is indeed the Update Catalog’s home. But a search on KB5000736 comes up dry. So MS is not offering this enablement package directly from the catalog anymore. That does suggest that the answer to this article’s main question is “If it works, then it’s good; if not, then it’s not.”
Expect the Best, But Prepare for the Worst
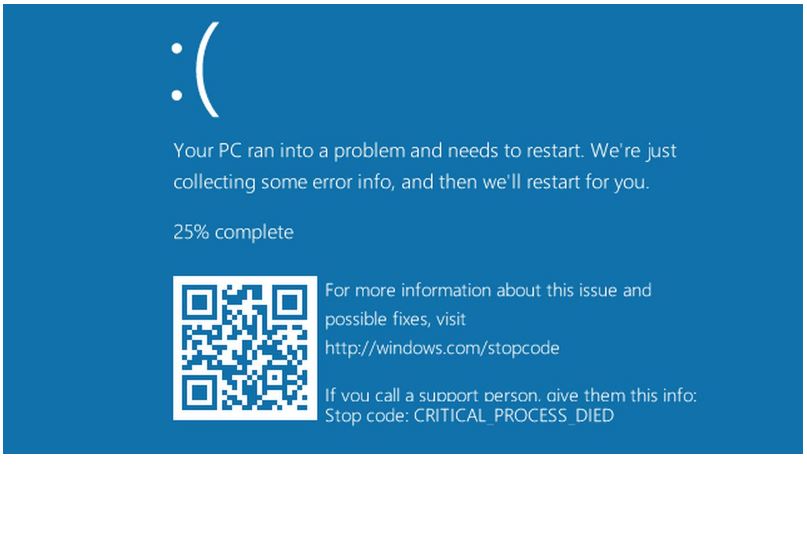
Because MS isn’t providing the enablement package directly as a catalog download, that means MS wants you to wait for Windows Update to make the offer. If you choose (as I did) to skip the wait and grab the enablement package from an alternate source (ditto), you should follow the sub-title’s advice. That is, I’d recommend making an image backup before applying the MSU file. Then, if the upgrade fails, you can boot to repair/recovery media and replace the current, suspect image with a current, known good working replacement.
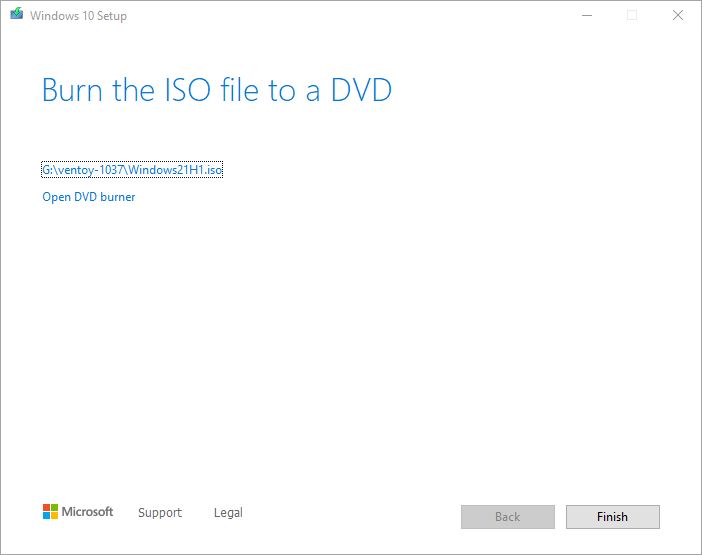
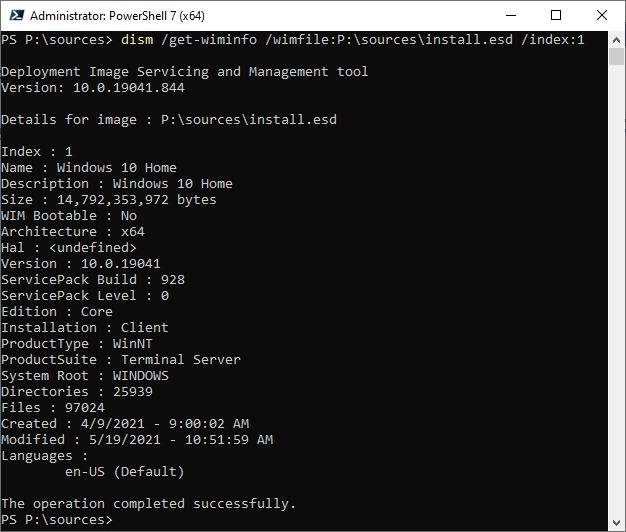
The ISO files for 21H1 are also available. The great appeal of the enablement package is that it’s blazing fast. If you do the ISO route, you’ll run setup.exe from its root folder and it will be a typical upgrade. The experience takes at least 15 minutes to complete, and leaves the Windows.old folder hierarchy around so you can roll back to 20H2 or 2004 as you might like. In that way, it may be “safer” than forcing the enablement package onto a PC. That’s because recovery from failure will be automatic, and you can even elect to roll back up to 10 days afterward if you decide you don’t like where 21H2 takes your PC.
Same Question, Different Answer
Another way to ponder the question “Is Forcing Win10 Upgrades Good?” is to try it, and see what happens. If it works, then yes. If it doesn’t, not only is the answer no, but your subsequent experience will depend on whether or not your pre-planning includes a recovery path. If it doesn’t the answer is “No, and it’s a PITA;” if it does, the answer is “No, but it didn’t take too long or hurt too much.”
And that, dear readers, is the way things sometimes go here in Windows World. it also explains why I still haven’t forced the enablement package onto my production PC just yet. I’m still thinking…