A routine UEFI firmware update brought unexpected trouble to the Flo6 system yesterday. What should have been a simple BIOS flash turned into a boot failure. The cause? A major change in Secure Boot keys. This event highlights how firmware updates can affect system trust and stability. As I was figuring out how UEFI flash overturned Flo6, I had to work my way through another CMOS reset, GPU disconnect, and more. Buckle up: here come the deets!
How UEFI Flash Overturned Flo6, and Killed Normal Boot-up
The BIOS update for Flo6 included more than microcode or AGESA changes. It replaced the Secure Boot Platform Key (PK), Key Exchange Key (KEK), and the Allowed Signatures Database (DB). These new keys came from Microsoft’s 2023 certificate chain. They replaced the older 2011 certificates that had been in use since Windows 8. This was a full trust-chain rollover, not a routine patch.
Why Did Boot Balk Afterward?
After the update, Flo6 failed to boot. The reason was a mismatch between the new firmware keys and the bootloader signatures. Windows had already staged boot components signed with the 2023 certificates. But the firmware update reset the trust chain. The system no longer recognized the bootloader as valid. Secure Boot rejected it, and the system dropped into firmware setup.
Recovery and Realignment
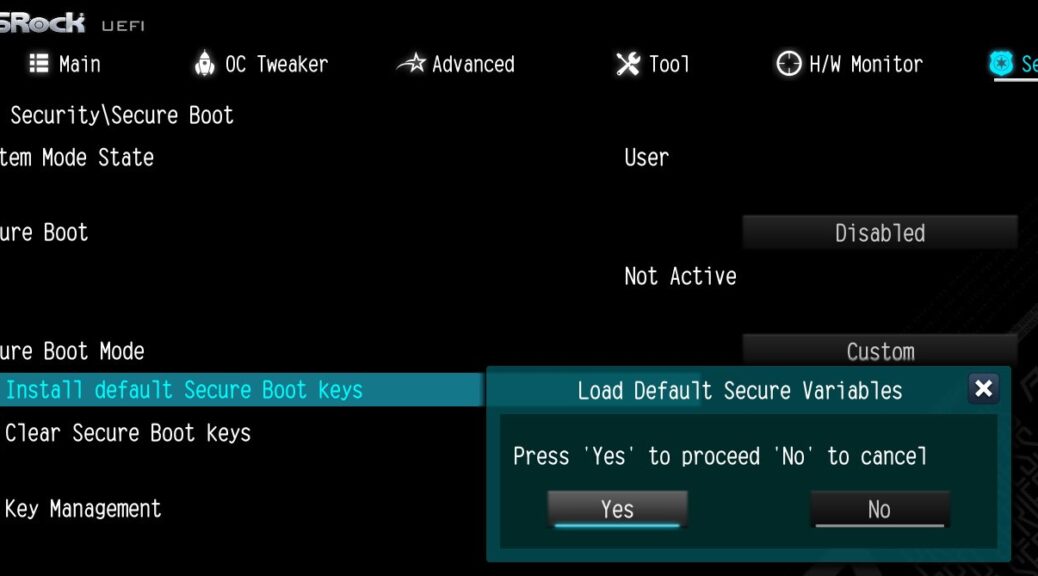
Once the firmware finished installing those new keys, Windows rebuilt its boot entries. It aligned its bootloader with the new DB. The system re-entered User Mode and Secure Boot resumed normal operation. Flo6 booted successfully again. The trust chain was restored, and the system stabilized.
Along that seemingly simple path, however, I had to reboot Flo6 at least a dozen times. Maybe more than that: I kinda lost count. At one point I had to pop the CR2032 CMOS battery. At another, I unpowered the GPU so the system would be forced to reset GOP stuff during a next restart, destined and designed to fail. Along the way I worked through nearly ever aspect of the ASRock board’s Secure Boot capabilities, setting things back to rights.
Lesson Learned
Firmware updates that modify Secure Boot keys are not routine. They change the foundation of system trust. If the OS and firmware are not aligned, boot issues can result. Understanding how PK, KEK, and DB work helps prevent surprises. Always check BIOS release notes for Secure Boot changes before flashing.
The Flo6 incident shows how a UEFI flash can affect more than performance or features. It can change the system’s trust model. With Secure Boot evolving, it’s more important than ever to understand what firmware updates really do.
Secure Boot has definitely made life more interesting here in Windows-World. I’ve just ordered an MSI MAG Tomahawk B550 board to replace the ASRock model. Hopefully, it will show itself more robust in the face of Secure Boot changes. We’ll see…